IDENTITY ARCHITECTURE IN CYBERSECURITY: HOW IDENTITY SHAPES SECURE SYSTEMS

There was a time when security leaned heavily on the network.
If you were outside the network, you were treated with suspicion. If you were inside the network, you were often treated as safer.
That was the thinking.
The office network was trusted.
The data centre was trusted.
The internal application was trusted.
The internal user was trusted.
The internal server was trusted.
A lot of security design was built around that idea.
Put important systems behind the firewall.
Separate the internal network from the public internet.
Control remote access.
Protect the perimeter.
Keep attackers outside.
For a long time, this made sense.
Systems were more contained. Users mostly worked from offices. Applications lived in controlled environments. Infrastructure was easier to map. The boundary between inside and outside looked clearer.
But modern systems do not behave like that anymore.
A user may be working from home.
A service may be running in the cloud.
A workload may be inside a container.
An API may be called by another system.
A third party may send data into the platform.
A SaaS tool may process business information.
An AI component may retrieve context from several sources.
A deployment pipeline may change production infrastructure.
So where is the trusted network now? That is the uncomfortable question.
Because in modern security, the network no longer carries the full weight of trust.
Identity does. Identity is now one of the most important parts of secure system design.
Every action in a modern system has an identity behind it.
A user signs in.
A service calls an API.
A workload requests access to a database.
An administrator changes a configuration.
A pipeline deploys code.
A third party sends a payload.
An AI component retrieves information.
A background process updates a record.
Something is always acting. Someone or something is always making a request.
That means the system has to answer some serious questions.
Who is this?
How do we know?
What are they allowed to do?
What should they never be able to do?
How long should this access last?
Can this action be traced?
What happens if this identity is compromised?
That is where identity architecture starts to matter.
Because if identity is unclear, nothing else is reliable.
Access decisions become weak.
Monitoring loses meaning.
Controls become harder to place.
Governance becomes messy.
Incident response becomes slower.
Risk becomes harder to explain.
A system can have good tools and still have a poor identity architecture.
A platform can have strong authentication at the front door and still allow services, workloads and automation to move around with too much privilege.
That is why identity needs to be treated as architecture.
Not just administration, user management or just IAM configuration.
Identity is part of the structure of the system.
Why network location used to carry so much trust
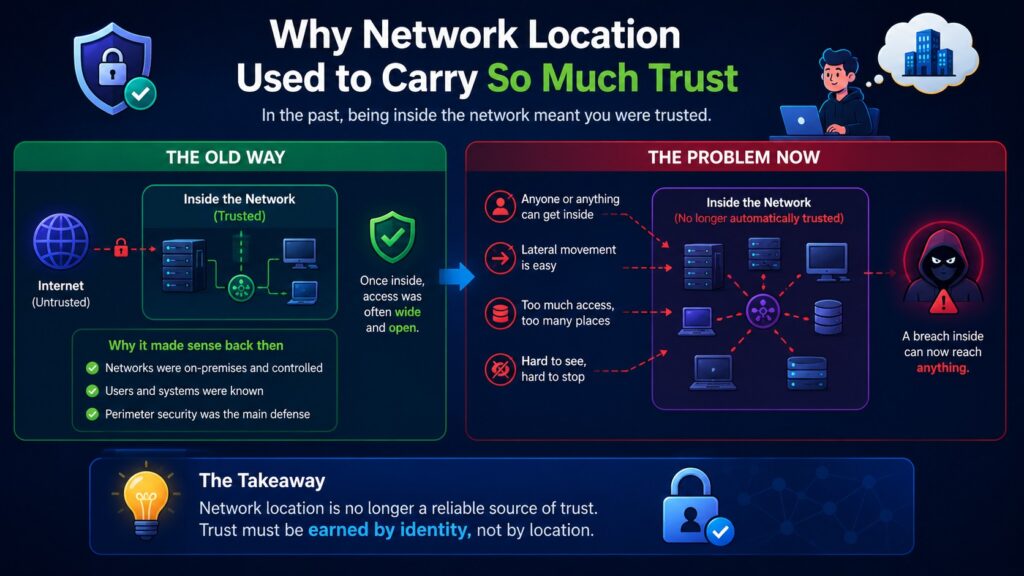
Older security models often treated location as a major signal of trust.
If traffic came from inside the corporate network, it was usually seen as safer.
If an application was internal, it was treated differently from one exposed to the internet.
If a server sat in a controlled environment, many teams assumed it carried lower risk.
This shaped how systems were designed.
External users had to prove who they were.
Internal users often had fewer checks.
External traffic went through stronger controls.
Internal traffic sometimes moved with less scrutiny.
Remote access was tightly managed, but once someone got inside the network, many systems behaved as though the hardest part was over.
That model created a kind of quiet confidence.
The firewall became the main line of defence.
The internal network became the safer zone.
The data centre became the place where important systems lived.
The perimeter became the thing everyone focused on.
But the problem with this model is simple.
Being inside does not mean being safe.
A compromised internal user is still a risk.
A compromised service is still a risk.
A misconfigured workload is still a risk.
A stolen token is still a risk.
An over privileged account is still a risk.
A trusted integration can still be abused.
Modern systems expose this weakness very quickly.
The old network boundary has become too thin to carry the level of trust placed on it.
That does not mean network controls no longer matter. They still matter.
Segmentation matters.
Ingress and egress controls matter.
Private connectivity matters.
Firewall rules matter.
Cloud network design matters.
But they are no longer enough on their own. Security decisions now need stronger identity context.
The system needs to know who or what is acting, not only where the request came from.
Modern systems are full of identities
When people hear identity, they often think of users. That is understandable.
Users log in.
Users have accounts.
Users have passwords.
Users use multi factor authentication.
Users get assigned roles.
But modern systems have many more identities than human users.
Services have identities.
Workloads have identities.
Applications have identities.
APIs have identities.
Pipelines have identities.
Administrators have identities.
Devices have identities.
Third party integrations have identities.
AI agents and automation flows may also need clear identities.
This is where many systems become difficult to govern.
The human identity model may be quite mature. But the service identity model may be vague.
The admin identity model may be too broad. The workload identity model may depend on shared secrets.
The integration identity model may have access that no one has reviewed properly for years.
This is how identity risk grows quietly.
Not always through one dramatic failure but more often through accumulation.
A service account is created quickly during delivery.
A workload is given broad access because the exact permissions are not clear yet.
An API key is shared between components.
A third party integration keeps access long after the original business need has changed.
An admin role is assigned to make delivery easier and never reduced.
A deployment pipeline can change more than it should.
Everything works.
The application runs.
The team delivers.
The platform passes basic checks.
But under the surface, identity has become messy.
And when identity becomes messy, security becomes messy.

Identity is behind every action
A secure system should not only care that an action happened. It should care who or what performed it.
That difference matters.
A record was accessed. By whom?
A configuration was changed. By which identity?
A service called another service. Using what credential?
A workload read from a data store. Was that access expected?
A pipeline deployed a change. Was that pipeline authorised to touch that environment?
A support user viewed customer information. Was that access justified?
An AI component retrieved sensitive context. Which identity allowed that retrieval?
This is where identity becomes the thread running through the whole system.
Without identity, actions become difficult to understand.
You may see activity, but not meaning.
You may see traffic, but not accountability.
You may see access, but not whether it was appropriate.
That is why identity architecture connects directly to visibility and governance.
If the system cannot tie activity back to clear identities, then monitoring is weaker than it looks.
Logs may exist, but they may not answer the questions that matter.
Who acted?
What did they access?
Was the access allowed correctly?
Was the permission too broad?
Was the identity expected to behave that way?
Was the activity normal for that role, service or workload?
Good identity architecture makes these questions easier to answer.
Poor identity architecture leaves teams guessing.
Authentication and authorisation are not the same thing
This is one of the areas where confusion causes real security weakness.
Authentication and authorisation are related, but they are not the same.
Authentication asks: Who are you?
Authorisation asks: What are you allowed to do?
A user can be successfully authenticated and still not be authorised to access a particular function.
A service can prove its identity and still have no valid reason to call a sensitive API.
A workload can be genuine and still be blocked from reading a database.
Authentication proves identity. Authorisation controls access.
Both have to work together.
If authentication is weak, the system may accept the wrong identity.
If authorisation is weak, the system may give the right identity too much access.
That second issue is very common.
Teams spend a lot of time making sure users can log in securely. Then access rules become broad, inconsistent or poorly reviewed.
A user gets access through a group that is too wide.
A service account can call more APIs than it needs.
A workload can read more data than its function requires.
An administrator has standing privilege when temporary privilege would be safer.
A third party integration can perform actions beyond its business purpose.
The system may still have authentication. But the access model is weak.
That is why identity architecture must cover both authentication and authorisation.
It should define how identities are established and how access is granted, limited, reviewed and removed.
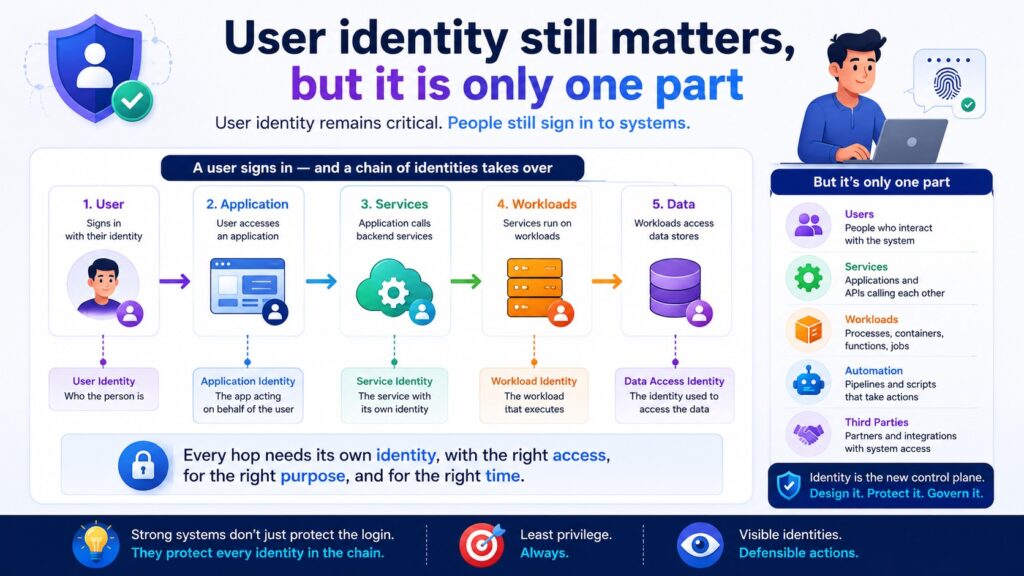
User identity still matters, but it is only one part
User identity remains critical. People still sign in to systems.
They still access data. They still perform business actions. They still make changes that affect risk.
So user identity must be designed properly.
That means clear authentication standards.
Strong multi factor authentication where risk requires it.
Sensible session management.
Role design that reflects real business responsibilities.
Access reviews that actually mean something.
Joiner, mover and leaver processes that work.
Privileged access that is controlled and monitored.
But user identity should not be designed in isolation.
A user does not act in a vacuum.
A user interacts with applications.
Applications call services.
Services call other services.
Workloads access data.
Administrative paths change the platform.
Automation makes decisions.
If user identity is strong but everything after the user is vague, the system still has a problem.
For example, a user may authenticate properly into an application.
But once inside, the application may use a highly privileged service account for all database access.
In that case, the user identity is strong at the front door, but the downstream identity model is weak.
The system may not be able to clearly distinguish what different users did at the data layer.
That affects auditability. It affects least privilege, incident response and governance.
This is why identity architecture has to follow the action through the system.
From user to application.
From application to service.
From service to workload.
From workload to data.
From data access to logging.
From logging to governance evidence.
That is how identity becomes useful across the full architecture.
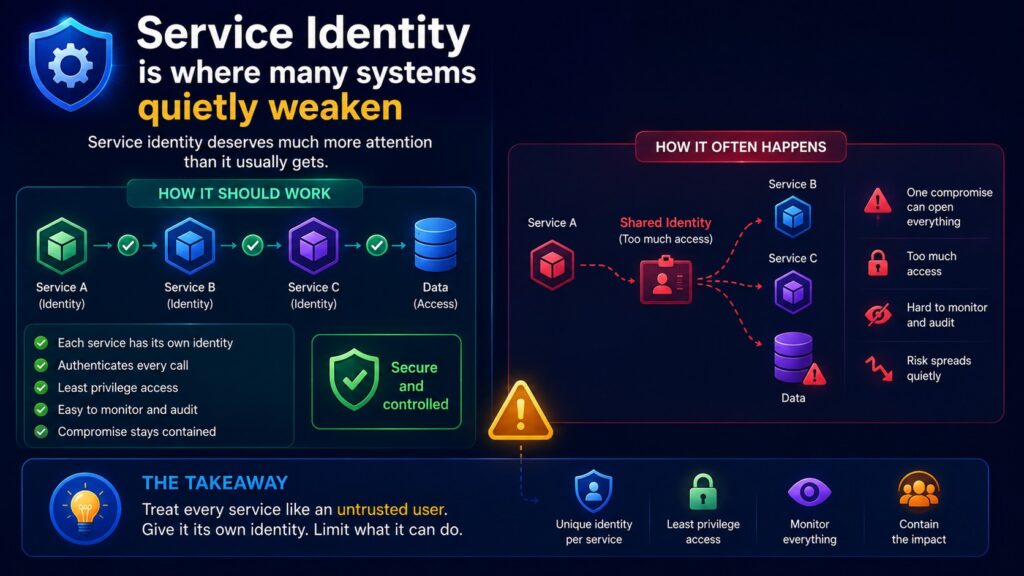
Service identity is where many systems quietly weaken
Service identity deserves much more attention than it usually gets.
In modern platforms, services constantly speak to other services.
An API calls another API.
A backend service calls a payment provider.
A microservice retrieves customer records.
A background worker reads from a queue.
A serverless function updates a store.
A container connects to a secrets manager.
A workflow engine triggers downstream processing.
All of these interactions need identity.
The calling service should have an identity.
The receiving service should know what identity is calling it.
The request should be authenticated. The action should be authorised.
The access should be scoped. The activity should be logged.
This sounds obvious, but many systems do not operate with that level of clarity.
Instead, service access often grows through convenience.
A shared secret is used by several services.
A token is accepted too broadly.
A service account has permissions across too many resources.
Internal calls are trusted because they come from inside the environment.
One service can call another without strong verification.
A workload uses long lived credentials because that was easier to implement at the time.
These things do not always break the system immediately.
That is why they survive. But they weaken the architecture.
If one service is compromised, the attacker may inherit the reach of that service identity.
If that identity is too broad, the blast radius becomes much larger.
A compromised service may be able to call other services, retrieve data, trigger actions or move deeper into the platform.
That is why service identity is central to zero trust identity and cloud identity security.
A service should not be trusted just because it is internal.
A workload should not receive broad access just because it needs to function.
An API should not accept calls without knowing who is calling and what that caller is allowed to do.
Service identity should be deliberate.
Named.
Scoped.
Rotated where needed.
Observable.
Owned.
Reviewed.
Tied to clear business and technical purpose.
If service identity is unclear, internal trust becomes uncontrolled trust.

Workload identity matters in cloud platforms
Cloud has changed how identity works.
In traditional environments, identity was often tied to users, servers and directories.
In cloud environments, identity is also tied to workloads.
A workload may be a virtual machine.
A container.
A serverless function.
A managed service.
A deployment process.
A data processing job.
An AI retrieval component.
These workloads often need access to cloud resources.
Storage.
Databases.
Queues.
Secrets.
Keys.
Logs.
APIs.
Configuration.
Monitoring tools.
The question is not only whether the workload can connect.
The question is what identity it uses when it connects.
This matters because cloud permissions can be very powerful.
A poorly scoped workload identity can expose data, change infrastructure, retrieve secrets or trigger actions across environments.
Many cloud incidents become worse because identities are over privileged.
The initial weakness may be small. But the identity attached to the workload gives access to far more than expected.
That is where cloud identity security becomes architecture.
A secure design should ask:
What workload is performing this action?
Does it need this access?
Can the access be narrower?
Can the permission be environment specific?
Can access be temporary?
Can secrets be removed from the design?
Can the identity be monitored?
Can unusual behaviour be detected?
Can the blast radius be contained?
These are not minor implementation details.
They shape how secure the cloud platform really is.
Good IAM architecture design makes workload access understandable and defensible.
Poor IAM architecture design leaves too much power hidden inside technical plumbing.
Identity across systems is where governance gets difficult
Most organisations do not run one neat system.
They run many systems.
Cloud platforms.
SaaS tools.
Internal applications.
Legacy systems.
Data platforms.
Analytics tools.
Security tools.
DevOps pipelines.
Third party services.
AI enabled components.
Identity has to work across this whole picture.
That is where things get difficult.
A user may exist in one directory.
A SaaS tool may have its own role model.
A cloud platform may have its own IAM structure.
A legacy application may use local accounts.
An integration may use API keys.
A third party may use shared credentials.
A pipeline may use service principals.
A workload may use managed identity.
Each part may work in isolation. But the overall identity picture may still be unclear.
This creates practical problems.
Who owns the identity?
Where is access approved?
Where is access removed?
Which system is the source of truth?
How are roles mapped across platforms?
How do we know whether access is still needed?
How do we trace activity across different systems?
How do we prove to governance that access is controlled?
This is why identity architecture cannot stay inside one tool.
It has to define how identity works across the system landscape.
That includes federation, role mapping, privilege boundaries, service identities, access reviews, logging and ownership.
Otherwise, identity becomes fragmented. And fragmented identity creates fragmented security.
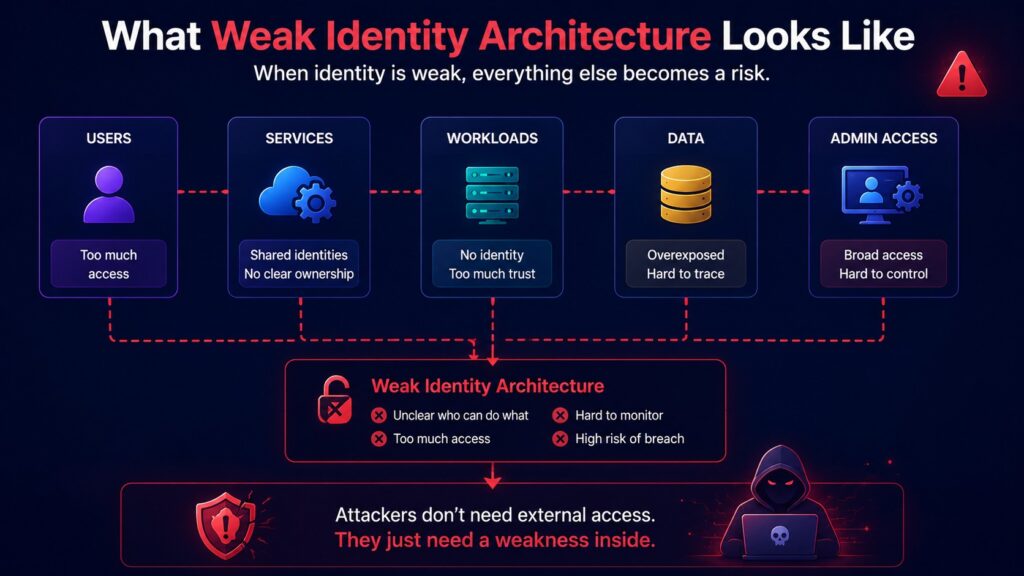
What weak identity architecture looks like
Weak identity architecture often looks normal on the surface.
People can log in.
Services can connect.
Systems can exchange data.
Delivery continues.
But the deeper questions are harder to answer.
Who owns this service account?
Why does this workload have access to that database?
Which roles can approve payments?
Which administrators have production access?
Which third party accounts are still active?
Which identities can retrieve secrets?
Which pipelines can deploy to production?
Which identities can access sensitive data across environments?
If those questions are difficult to answer, there is already an identity architecture problem.
Common signs include:
Too many shared accounts.
Service accounts with no clear owner.
Long lived secrets.
Broad administrator access.
Roles that do not match real responsibilities.
Access granted for delivery and never reduced.
Poor separation between environments.
Weak logging of identity activity.
Inconsistent use of multi factor authentication.
APIs trusting internal callers too easily.
Workloads using permissions that are wider than needed.
Third party integrations with excessive access.
These weaknesses may not cause immediate failure.
But they create fragile conditions.
When something goes wrong, the organisation discovers that it cannot confidently explain who had access, what they could do, and what actually happened.
That is not where any organisation wants to be during an incident, audit or governance review.
Identity and trust boundaries belong together
Identity architecture connects directly to trust boundaries.
Every time trust changes, identity should become clearer.
When a user enters an application, identity matters.
When an application calls an API, identity matters.
When one service calls another, identity matters.
When a workload requests data, identity matters.
When an administrator performs a privileged action, identity matters.
When data leaves the platform for a third party, identity matters.
Trust boundaries show where verification needs to happen.
Identity shows who or what is being verified.
This is why trust boundary design and identity architecture should not be separated.
If the trust boundary is clear but the identity model is vague, access decisions will still be weak.
If the identity model is clear but the trust boundaries are vague, the system may still apply controls in the wrong places.
They need each other.
A good security architecture asks:
Where does trust change?
What identity is used at that point?
How is that identity proven?
What access is allowed?
What access is denied?
What should be logged?
What happens if that identity is compromised?
That is how identity becomes part of secure system structure.

Identity and least privilege
Least privilege is one of those phrases everyone agrees with.
The difficulty is making it real.
You cannot design least privilege properly if identity is unclear.
Because least privilege depends on knowing who or what needs access, what they need it for, and where that access should stop.
For a user, this may mean access based on role, responsibility and business need.
For a service, it may mean permission to call only specific operations.
For a workload, it may mean access to one data store, not the whole environment.
For an administrator, it may mean temporary access for a specific task.
For a pipeline, it may mean deployment rights only to the right environment.
The principle is simple.
Access should match purpose.
But in real systems, this takes discipline.
Teams need to avoid giving broad access just to keep delivery moving.
They need to revisit temporary access.
They need to separate duties.
They need to remove permissions when roles change.
They need to stop treating internal identities as automatically safe.
Least privilege is not only a control. It is a design habit.
And identity architecture is what makes that habit possible.
Identity and observability
A system that cannot observe identity activity cannot govern access properly.
It is not enough to know that something happened.
The system needs to know which identity was involved.
That applies to:
User sign ins.
Failed authentication attempts.
Privilege changes.
Role assignments.
Service calls.
Token usage.
Secrets access.
Admin actions.
Data access.
Cross environment activity.
Third party integration calls.
Pipeline deployments.
Identity logs should help answer real questions.
Was this identity expected to act this way?
Was this access normal?
Was this role recently changed?
Was this service account used outside its expected pattern?
Was this workload accessing data it does not usually touch?
Was an administrator using standing privilege?
Was a third party integration active outside agreed behaviour?
Without this context, monitoring becomes much weaker.
You may collect logs, but still struggle to understand risk.
Good identity observability supports incident response, assurance, governance and operational control.
It also gives security architects evidence. And evidence matters.
Architecture that cannot be evidenced becomes difficult to defend.
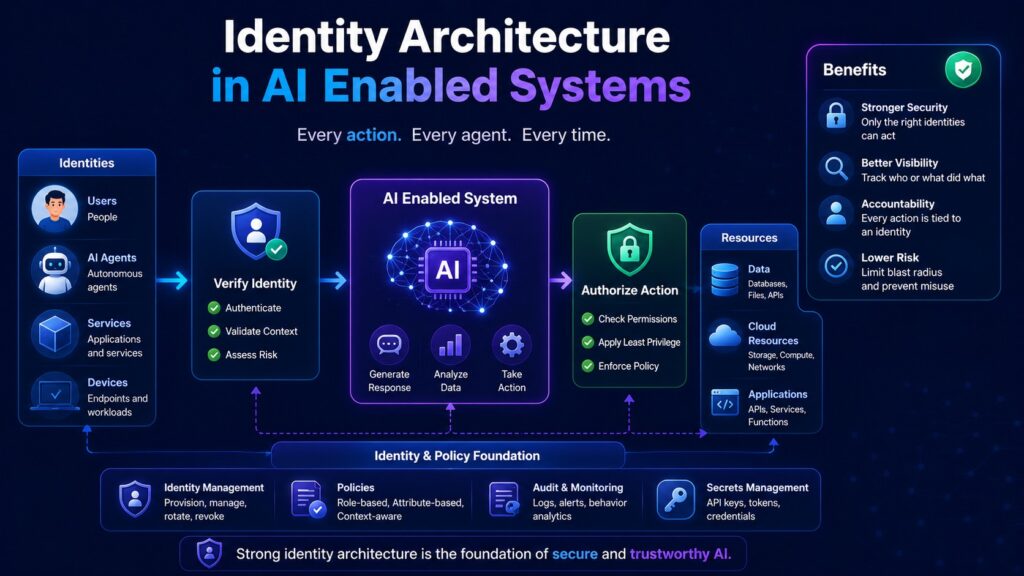
Identity architecture in AI enabled systems
AI enabled systems introduce another layer of identity complexity.
A user may ask a question.
The AI component may retrieve data.
A model may generate an output.
An agent may trigger an action.
A workflow may update another system.
Each step needs identity clarity.
Who is the user?
What data is the AI component allowed to retrieve?
Is it acting under the user’s permissions?
Does it have its own service identity?
Can it access sensitive records?
Can it call downstream tools?
Can it trigger business actions?
Can the output influence decisions?
Can the activity be logged and reviewed?
AI systems can become risky when their identities and access paths are vague.
If an AI component can retrieve too much data, the exposure risk grows.
If an AI agent can perform actions without clear authorisation, operational risk grows.
If model activity is not traceable, governance becomes weak.
The same architecture discipline applies.
Define the trust boundaries.
Define the identities.
Scope the access.
Log the actions.
Review the decisions.
Keep human oversight where it matters.
Implicit trust in AI behaviour is not acceptable.
AI components need structural control, just like traditional platforms.
Where The Blueprint Method™ fits
This is where The Blueprint Method™ fits naturally.
The Blueprint Method™ is a Secure by Design security architecture framework developed by Cyb Uranus.
It provides a structured way to design platforms where security is engineered into the architecture from the beginning.
Modern digital platforms are complex systems.
Cloud infrastructure, APIs, SaaS platforms, distributed applications and AI components all interact across multiple environments.
Data moves constantly. Identity travels across services.
Decisions are made by humans, applications, workloads and automated systems.
In many organisations, security still enters the conversation too late.
A system is designed.
A platform is built.
A programme moves into delivery.
Then security appears as a review. Controls are added after the architecture already exists.
That approach creates fragile systems. Security becomes reactive.
Cyb Uranus approaches this differently.
Security is engineered into system structure from the beginning.
The Blueprint Method™ defines:
Explicit trust boundaries.
Identity models.
Structured control placement.
Documented architectural decisions.
Governance aligned security design.
Operational observability.
Identity is a core part of this.
Because a platform cannot be secure by design if it cannot explain who or what is acting inside it.
The Blueprint Method™ examines systems across five structural layers.
Business.
Data.
Application.
Technology.
Operations.
The identity questions appear across every layer.
At the business layer, who needs access and why?
At the data layer, which identities can reach sensitive information?
At the application layer, how are authentication and authorisation enforced?
At the technology layer, how are workloads, services and infrastructure identities controlled?
At the operations layer, can identity activity be observed, reviewed and evidenced?
That is how identity becomes architecture.
Not just account management and access administration.
A structural part of how the platform works.
How the Security Architect’s Blueprint supports identity design
Security architecture often fails when it becomes documentation that delivery teams cannot use.
Large documents are written. Diagrams are produced. Controls are listed.
But when delivery pressure arrives, the architecture disappears.
The Security Architect’s Blueprint was created to solve that problem.
It provides a practical system for designing Secure by Design enterprise platforms that remain defensible, reviewable and usable in real delivery environments.
For identity architecture, this matters because identity decisions must be traceable.
Why was this access model chosen?
Why does this service need this permission?
Why is this workload allowed to access this data?
Why does this administrator need privileged access?
How is access reviewed?
How is activity evidenced?
How does the identity model support governance?
The Security Architect’s Blueprint helps connect these decisions to architecture, governance and assurance.
It supports:
Security architecture documentation.
Identity and access model definition.
Trust boundary analysis.
Control baselines.
Security non functional requirements.
Architecture decision records.
Threat modelling.
Implementation checklists.
Assurance and evidence tracking.
That matters in real enterprise environments.
Because identity architecture has to survive more than design discussions.
It has to survive delivery pressure.
It has to survive governance boards.
It has to survive audit.
It has to survive incident response.
It has to be clear enough for engineering teams to implement.
It has to be structured enough for risk teams to review.
It has to be practical enough for operations teams to monitor.
That is the difference between identity as an idea and identity as a working security control.
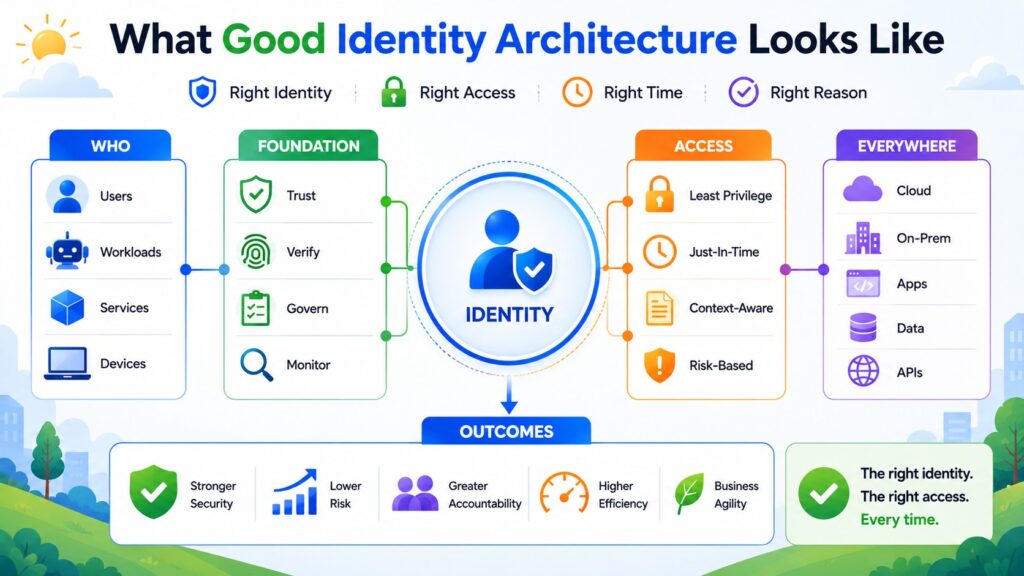
What good identity architecture looks like
A strong identity architecture is clear.
You can explain it, evidence it, operate it and govern it.
It should show:
Who the main identities are.
How users authenticate.
How services authenticate.
How workloads authenticate.
How authorisation decisions are made.
How privileged access is controlled.
How third party access is managed.
How access is reviewed.
How identities are logged and monitored.
How access is removed.
How identity risks are accepted or remediated.
It should also be realistic.
There is no point designing an identity model that looks perfect on paper but cannot be implemented by the team.
Good architecture has to work under real conditions.
Delivery pressure.
Legacy constraints.
Cloud complexity.
SaaS limitations.
Operational support needs.
Regulatory expectations.
Audit requirements.
Incident response demands.
This is why proportionate control matters.
Controls should reduce identifiable risk without creating unnecessary operational complexity.
Over engineering wastes capacity. Under engineering invites compromise.
Precision creates resilience.
Final thought
Identity architecture is now one of the clearest signs of whether a system has been designed with discipline.
Modern systems are no longer protected by network boundaries alone.
Users move.
Services interact.
Workloads run across platforms.
APIs expose business functions.
Data travels.
Automation acts.
AI components retrieve and influence information.
Every meaningful action has an identity behind it.
If that identity is clear, the system can make better decisions.
If that identity is vague, everything becomes harder to trust.
Authentication becomes weaker.
Authorisation becomes broader.
Access reviews become messy.
Monitoring loses context.
Incident response becomes slower.
Governance becomes harder to defend.
That is why identity architecture matters so much in cybersecurity.
It shapes how access works.
It shapes how trust is verified.
It shapes how services interact.
It shapes how workloads reach data.
It shapes how actions are traced.
It shapes whether the platform can remain secure and governable as it grows.
Security architecture cannot treat identity as a side topic.
Identity sits at the centre of modern secure system design.
And for organisations building cloud platforms, distributed systems, API ecosystems and AI enabled services, this needs to be addressed from the beginning.
That is exactly why Cyb Uranus developed The Blueprint Method™ and the Security Architect’s Blueprint.
To help organisations design systems where trust boundaries, identity models, control placement, governance and operational visibility are built into the structure of the platform.
Security should not appear late as a review.
It should be engineered into the system from the start.
Because when identity is clear, security has something solid to stand on.
When identity is unclear, nothing else is reliable.
Need help designing identity architecture that holds in real systems?
If you want secure architecture that is clear, practical, governance ready and built for modern cloud, API, distributed and AI enabled environments:
Explore The Blueprint Method™
Get the Security Architect’s Blueprint
View Secure-by-Design Advisory Service
Request a conversation
Learn more about Cyb-Uranus

