HOW SECURITY ARCHITECTS DESIGN SECURE SYSTEMS IN MODERN ENVIRONMENTS

Where secure systems actually begin
A secure system usually begins long before anyone talks about controls.
It begins when a team starts shaping a service, a platform, an integration, or a workflow.
It begins when someone decides which components will exist, where data will sit, how users will interact, which services will trust each other, and what has to happen for the system to deliver its purpose.
That is the point many people miss.
They assume security starts when someone introduces encryption, monitoring, policy requirements, or access restrictions.
By that stage, a lot of the important decisions have already been made. The system already has a shape.
Paths between components already exist. Trust has already started settling into the design.
Data has already been given routes to travel. Privilege has already started gathering around certain services and people.
This is why the real work of security architecture starts early.
This is not because security needs to dominate every conversation nor should every design meeting become an assurance exercise.
It is because structure hardens quickly.
Once a system starts taking shape, people begin building to that shape. Teams integrate against it. Workarounds form around it. Delivery pressure builds around it. Then changing it becomes harder than it first looked.
That is where security architecture lives.
It lives in the structure of the system.
In the decisions that define how trust works.
In the choices that determine how access moves.
In the points where data is allowed to enter, be processed, be stored, and leave.
In the places where control can be enforced properly because the system was designed to support it.
That is the difference between a system that is secure by structure and a system that spends its life trying to compensate for weak early decisions.
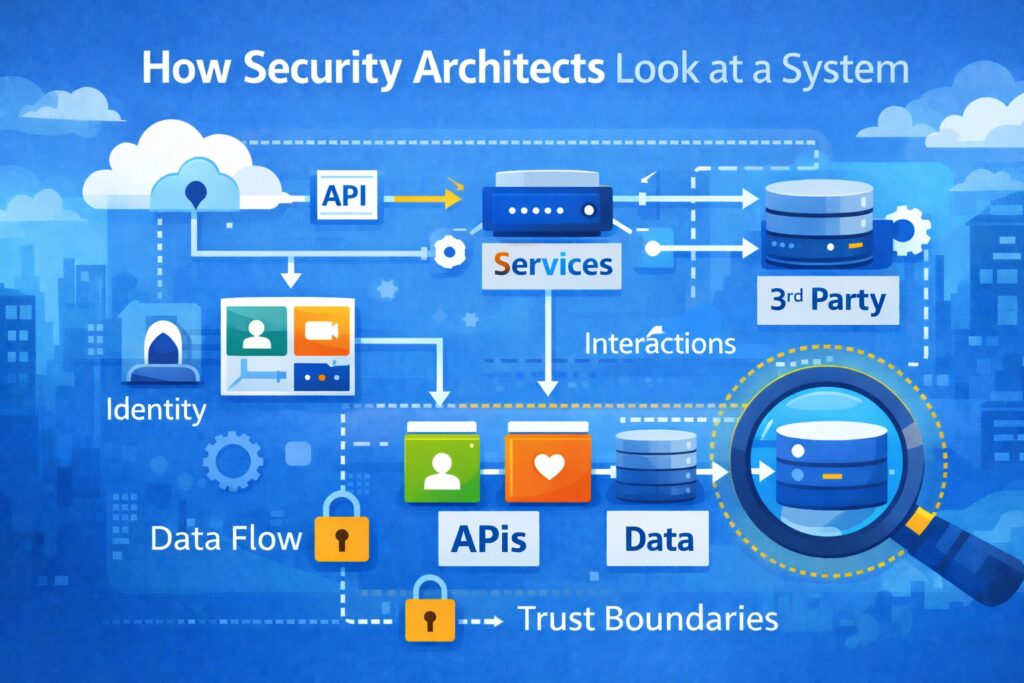
How Security Architects Look at a System
When I look at a system, I am not starting with a shopping list of products.
I am trying to understand behaviour.
What is this system here to do.
What matters inside it.
Who interacts with it.
Which parts of it carry trust.
How that trust moves.
What can reach what.
What happens when something fails.
What happens when a component behaves outside expectation.
A system is not just a diagram. It is a set of interactions that keep happening over time.
Users authenticate.
Applications call APIs.
Services exchange tokens.
Workloads access data stores.
Admins perform support actions.
Third-party systems consume or push data.
Logs and events are generated as all of this takes place.
That is where the truth sits.
A system may look neat in documentation and still behave in ways that weaken security.
A clean high-level diagram can hide over-permissioned services, weak separation between workloads, badly scoped support access, loose internal trust, unnecessary data movement, and blind spots in visibility.
This is why good cybersecurity architecture starts with clear observation.
You are trying to see the system as it will actually behave in operation, not just how it was described in a design workshop.
Once you do that, patterns appear quickly.
You see where access is likely to spread.
You see where trust is assumed without enough basis.
You see where data could travel further than anyone intended.
You see where control placement will matter.
You see where visibility might disappear once the platform is live.
That is the beginning of the security architecture design process.
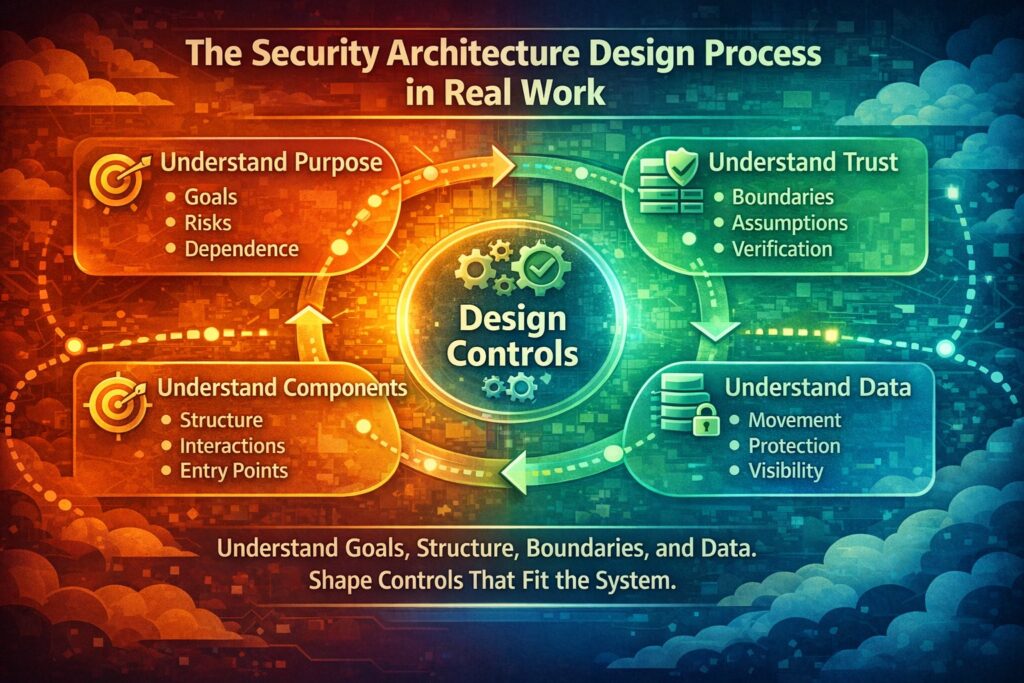
The Security Architecture Design Process in Real Work
The security architecture design process is sometimes presented as a simple sequence.
Real projects are not that tidy.
Still, there is a clear logic underneath the work.
First, you need to understand purpose.
What is the system for?
What business outcome does it support?
What would matter if it failed?
Which users, teams, or external parties depend on it?
What kind of harm would matter most?
Then you need to understand what is actually being built.
What are the components?
How do they interact?
Where are the entry points?
What are the privileged paths?
Which services talk to which other services?
What dependencies sit outside the immediate platform?
Then you need to understand trust.
Where does trust begin?
Where should it stop?
What is being assumed?
What is being verified?
Which interactions need stronger control because compromise would have wider effect?
Then you need to understand data.
What data enters the system?
Which data is sensitive?
Which data is operationally important?
Where does it move?
Where is it copied?
Where is it transformed?
Where is it visible to systems or people that may not need full access?
Then you need to design control in a way that fits the structure.
- Identity
- Authentication
- Authorisation
- Segmentation
- Validation
- Secrets handling
- Monitoring
- Auditability
- Response and recovery
That is how security architects work when they are doing architecture, not just checking controls after the fact.
The point is not to create a large document full of abstract statements. The point is to shape the conditions that allow the system to remain controllable as it evolves.
Identity is where control starts to hold
Identity is one of the first things I want to understand in any modern platform.
Not just user identity.
Service identity matters.
Workload identity matters.
Administrative identity matters.
Automation identity matters.
Every meaningful action in a system should connect back to something known and governed.
A known user.
A known service.
A known workload.
A known operational process.
When that is missing, the architecture starts drifting almost immediately.
Shared accounts appear because they feel efficient.
Credentials get reused because delivery is moving quickly.
A backend process gets broad access because the narrower permissions were not designed clearly.
A support path stays too powerful because it was built for convenience during early delivery and never tightened later.
This is how access becomes difficult to reason about.
It stops being attached closely enough to purpose.
And when access is no longer close to purpose, it becomes harder to reduce, harder to review, and harder to trust.
You start seeing actions that cannot be confidently traced.
Permissions that cannot be justified cleanly.
Dependencies that rely on privilege no one fully understands.
Reviews that produce uncertainty instead of clarity.
In secure system design, identity is deliberate from the beginning.
Each component has its own identity and role.
Each role exists for a reason.
Authentication decisions are made where they matter.
Permissions reflect actual behaviour and actual need.
Service-to-service trust is explicit, not inherited casually.
That does not make systems simple. But it makes them governable.
And governable systems are much easier to protect over time.
What weak identity looks like in practice
Take a normal cloud platform.
Users sign in through a frontend.
The frontend calls backend APIs.
Those APIs communicate with internal services.
Services need access to storage, queues, databases, and third-party integrations.
Support teams need some operational access.
Automation processes need deployment or maintenance permissions.
Now imagine identity was never shaped properly.
The frontend passes a token downstream in ways that are trusted too broadly.
One service uses static credentials stored somewhere it should not.
Another service has excessive database privileges because narrowing them felt too difficult.
An admin path reaches across multiple environments without enough separation.
An integration account holds permissions that no longer match its current function.
This may not create immediate operational drama.
The platform may still perform well. Features may still ship. Users may still have a smooth experience.
But structurally, the system is already carrying hidden weakness.
Because a single compromised component could now expose too much.
A single token or credential might unlock more than intended.
A support path might give wider reach than governance would ever have approved if it were fully visible.
This is why identity is not just a technical implementation detail.
It is one of the main foundations of enterprise security architecture.
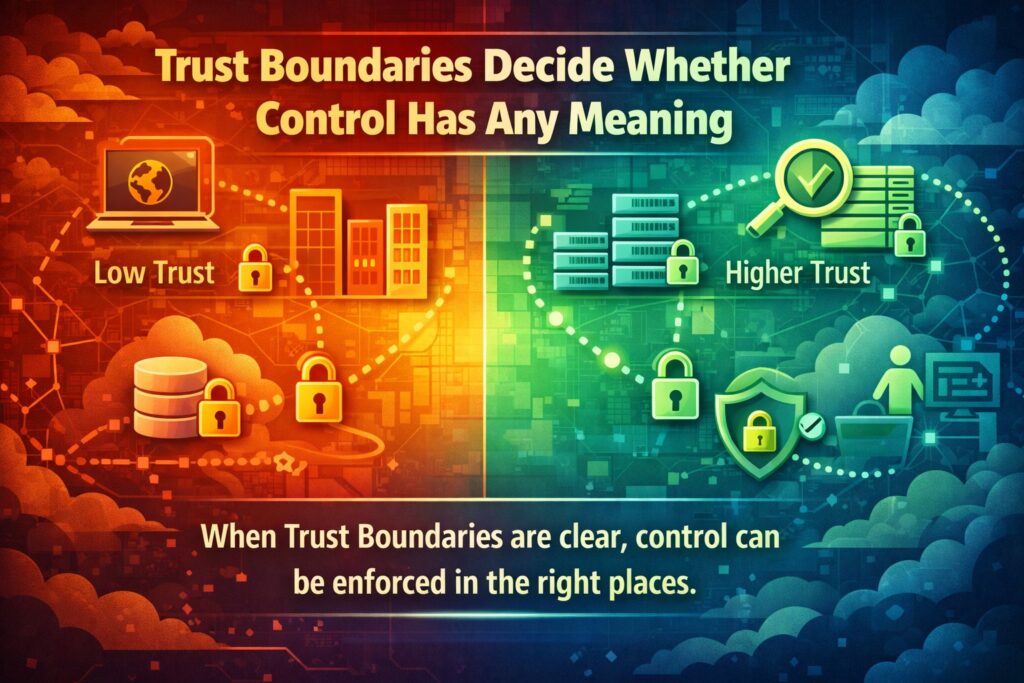
Trust boundaries decide whether control has any meaning
Trust boundaries are one of the clearest indicators of whether a system has been architected with care.
A trust boundary is simply a place where the level of trust changes and verification must mean something.
Between the public internet and an application.
Between one internal service and another.
Between one environment and another.
Between a workload and a sensitive data store.
Between an enterprise platform and an external provider.
Between automated processing and human administrative intervention.
If these boundaries are not explicit, the system starts behaving as though too many things are trusted by default.
That is where a lot of systems weaken.
An internal service gets treated as safe because it sits inside the platform.
A support component is trusted too broadly because it was built for convenience.
An environment intended for lower-risk processing becomes able to touch more sensitive paths.
A third-party integration gets wider access because constraining it would have required more design discipline.
Nothing may look obviously broken.
But containment begins to disappear.
And once containment becomes weak, one small compromise can travel further than anyone expected.
When trust boundaries are defined properly, you can make meaningful decisions.
Where authentication must happen.
Where authorisation must be checked.
Where filtering and validation must sit.
Where communication should be constrained.
Where visibility must be strongest.
Where movement across boundaries should trigger scrutiny.
That is how trust boundaries affect control.
They turn security from a vague aspiration into something that can be enforced in specific places.
Where systems usually begin to weaken
Most systems do not become insecure because one dramatic mistake was made in public view.
They usually weaken gradually.
A service is given wider access to move delivery along.
An API is opened up to support a dependency.
An operational path remains broader than it should because tightening it feels risky.
A shared data store is used by multiple components because it was expedient at the time.
A lower-risk environment becomes more connected than it was meant to be.
Each decision can sound reasonable on its own.
That is why these problems persist.
But systems are shaped by the accumulation of these decisions, not by how reasonable each one sounded when it was made.
Over time:
Trust becomes broader.
Identity becomes less precise.
Data moves more widely.
Controls become harder to place cleanly.
Dependencies become harder to change without fear of breakage.
Then a review takes place and teams discover that the system still works, but its structure now carries more risk than anyone is comfortable with.
This is where security starts to look expensive and frustrating.
This is not because security itself is the problem.
It is because the architecture was allowed to settle first, and now security is trying to tighten something that was never shaped to hold tightly.
Data flow reveals the truth of a system
If I want to understand what really matters in a system, I follow the data.
Where does it enter.
What creates it.
What enriches it.
What stores it.
What exports it.
What logs it.
Who can read it.
Who can modify it.
How long does it persist.
Data flow exposes things quickly.
You see sensitive information crossing more services than expected.
You see logging patterns that expose more than intended.
You see support tooling with access to data it never truly needed.
You see copies being created without a clear retention purpose.
You see external dependencies receiving more information than the business purpose justifies.
This is why data flow is one of the strongest anchors in secure system design.
Because data does not care about neat architecture slides. It moves according to what the system actually allows.
A team may think a platform has strong control because the core application is well protected. Then you trace the data and discover that the same information appears in logs, analytics feeds, exports, admin dashboards, support workflows, and third-party integration paths.
That is not a tooling problem first. It is an architecture problem.
Once data flow is understood clearly, control decisions get stronger.
You know where stronger protection is justified.
You know which services should not see full payloads.
You know where minimisation should happen.
You know where exposure risk is highest.
You know where retention and deletion need more discipline.
That is how data flow reveals the truth faster than many other architecture views.
What this looks like in a real platform
Consider a customer-facing platform.
A user submits information through a web application.
The application hands it to backend services.
Those services may validate, enrich, transform, and store the data.
Some parts of that data may be exported to partners, analytics tools, support systems, or workflow engines.
Now ask a few simple questions.
Does every service in that chain need the full dataset?
Do logs ever capture fields that should have been suppressed?
Can support teams view more than their function requires?
Are third-party integrations receiving only what is necessary?
Can sensitive fields be traced to every place they end up?
These are architecture questions.
They tell you whether the system has been shaped deliberately or has simply evolved into a wider exposure pattern over time.
When data flow is designed properly, the platform becomes easier to secure because the routes are intentional.
When it is not, risk begins to spread quietly through perfectly normal operations.
Control placement is where architecture becomes real
A lot of security conversations focus on whether a control exists. That is only part of the story.
Control placement matters just as much.
A control can exist and still fail to change the behaviour that matters.
Authentication at the edge may be useful.
If internal service trust is weak, that is not enough.
Encryption in storage may be useful.
If data is copied widely and exposed through application responses, it does not solve the real issue.
Monitoring may exist.
If it does not capture meaningful events at identity points, administrative paths, or trust boundaries, visibility will still be weak.
Control placement means asking where a control needs to sit so that it actually affects how the system behaves.
At the identity point.
At the API boundary.
At the service-to-service interaction.
At the data handling point.
At the administrative path.
At the observability layer.
At the deployment and change layer.
This is one of the most practical parts of the security architecture design process.
Because this is where theory turns into structure.
Poorly placed controls create false comfort.
Well-placed controls create predictable behaviour.
And predictable behaviour is what allows security to scale with the system.
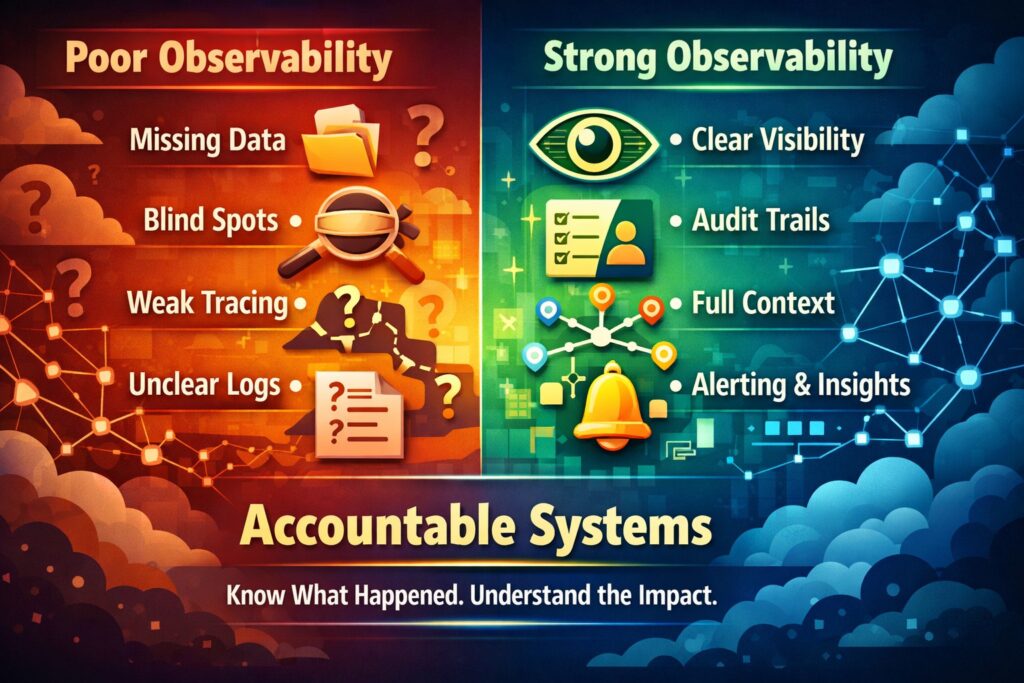
Visibility and observability keep the system accountable
A system that cannot be observed properly cannot be governed properly.
You need to know what happened, who did it, where it happened, what changed, and how that activity crossed meaningful boundaries.
Without that, assurance becomes guesswork.
Logging and monitoring are often discussed too late. Teams assume they can be added when the platform is almost ready.
That usually creates weak observability.
Critical events are not captured cleanly.
Administrative actions are poorly traced.
Cross-service activity cannot be reconstructed easily.
Security-relevant context is missing from logs.
Events exist, but they do not answer the questions that matter during review or incident response.
In well-designed systems, visibility is part of the architecture.
Identity-related events are meaningful.
Service interactions can be traced.
Administrative activity is visible enough to review.
Key decision points generate usable evidence.
Monitoring aligns with the parts of the system where trust and risk actually change.
This matters for security. It also matters for operations, governance, and resilience.
Because secure systems do not just need controls. They need to remain understandable once they are live.
How security architects work with delivery teams
There is still a common misunderstanding about how security architects work.
Some people picture a security architect as someone who appears late, reviews documentation, and blocks delivery.
That is not how good architecture work looks.
A good security architect spends a lot of time asking clear questions early enough to shape decisions before they harden.
Where are the real trust boundaries?
Which interactions need stronger verification?
What identity model will actually hold here?
How should data move?
Where should controls sit so they fit the architecture?
How will this be observed once it is live?
What happens if this dependency fails or behaves unexpectedly?
What access will support teams need?
How will that access be constrained and reviewed?
This is collaborative work.
It sits close to engineering.
Close to platform design.
Close to delivery reality.
The point is not to make the design look theoretical. The point is to make it hold under operational pressure.
That is one of the best signs that security architecture is being done properly.
The design still makes sense when the project becomes busy.
When security comes in late
You can usually tell when security joined after the platform had already taken shape.
The signs are not always in the architecture deck.
They show up in behaviour.
Permissions are being adjusted repeatedly because the original access model was too broad.
Services are trusted in ways no one feels fully comfortable explaining.
APIs are exposed more widely because dependent components already rely on that reach.
Data exists in places that are difficult to clean up.
Support access remains broad because tightening it now would affect too many teams or workflows.
Then security reviews become reactive.
Issues are found.
Recommendations are made.
But each recommendation now has to work around existing structure.
That is where projects start saying things like:
We should have done this earlier.
Too many services depend on that now.
We can address part of it in a later phase.
We will need a risk acceptance for this one.
This is not always a sign of careless people. Often it is just what happens when architecture decisions settled before security had enough influence.
The system may still go live. It may still deliver value.
But the cost of improvement becomes higher because the platform now has history, dependencies, and operational habits built into it.
What changes when security is considered early
When security is present early enough, the whole character of the platform changes.
Identity does not have to be retrofitted later.
Trust boundaries do not need to be rediscovered after integrations are already live.
Data movement does not get normalised before anyone asks whether it should exist.
Observability is designed around real decision points, not guessed after the fact.
The result is not perfection. It is clarity.
Access stays closer to purpose.
Dependencies stay easier to reason about.
Teams know where controls belong.
Changes are easier to make safely.
Governance conversations become more grounded because architectural intent is visible.
This is one of the biggest advantages of secure-by-design thinking.
It reduces the amount of later correction the system will need.
That matters in modern environments because systems are already complicated enough before weak structure makes them harder.
What this looks like in cloud and distributed environments
Cloud platforms make all of this more visible because they create many interactions very quickly.
A modern platform may include:
A frontend application
Multiple APIs
Containers or orchestrated workloads
Serverless processing
Managed storage
Queues and event streams
Identity providers
Third-party integrations
Admin and support paths
Deployment pipelines
Monitoring and alerting services
This is not just a technology stack. It is a trust structure.
Every part introduces decisions about identity, access, communication, data movement, and observability.
If identity is inconsistent across these interactions, access expands without enough control.
If trust boundaries are vague, services start inheriting trust they were never meant to have.
If data flow is poorly understood, sensitive information spreads across perfectly ordinary operational paths.
If control placement is weak, the platform may appear mature while carrying serious blind spots between components.
This is why enterprise security architecture matters so much in cloud systems.
Because complexity grows quickly. And if structure does not keep up with that growth, risk does.

The five-layer thinking behind strong design
One practical way to keep architecture grounded is to examine the platform across five layers:
Business
Data
Application
Technology
Operations
This is not just a presentation model. It is a way of making sure important issues are not missed.
Business layer
What is the system here to do?
What would matter if it failed?
Who depends on it?
What business consequence or harm needs to shape the level of control?
A system processing public content has different needs from one handling regulated or sensitive case data. Security decisions should reflect that difference.
Data layer
What data exists?
How sensitive is it?
Where does it move?
Where is exposure highest?
Which parts of the platform truly need to see it?
This is where you understand what deserves stronger protection and why.
Application layer
How does the application enforce trust?
How are users authenticated?
How are services authorised?
How is input validated?
How are privileged operations handled?
This is where policy becomes actual system behaviour.
Technology layer
How is the environment segmented?
How are workloads isolated?
How do components connect?
How are infrastructure boundaries defined?
What allows or restricts lateral movement?
This layer affects containment directly.
Operations layer
Can activity be observed?
Can incidents be reconstructed?
Can changes be traced?
Can recovery happen with enough clarity?
Can governance bodies review meaningful evidence?
This layer determines whether the platform remains understandable once it is in use.
A platform is much easier to trust when all five layers have been considered clearly.
Where The Blueprint Method™ fits naturally
This is exactly where The Blueprint Method™ fits.
The Blueprint Method™ was built to bring structure to the design of secure systems from the beginning. It treats security as part of architecture, not as an external activity attached later.
That means starting with structure.
Understanding the system purpose.
Understanding the data.
Understanding the interactions.
Defining trust boundaries.
Designing identity models deliberately.
Placing controls where they fit the behaviour of the system.
Keeping observability and governance close to delivery.
The five-layer model inside The Blueprint Method™ gives teams a practical way to examine the platform fully across Business, Data, Application, Technology, and Operations.
That matters because secure systems do not fail in one narrow place. Weakness usually appears across relationships, assumptions, and accumulated design shortcuts.
The Blueprint Method™ helps make those things visible early enough to shape them.
Security architecture as a working discipline
Security architecture works best when it is treated as an active discipline inside delivery.
Not just as documentation.
Documents matter. Diagrams matter. Decision records matter. Assurance evidence matters.
But none of those replace the discipline of shaping systems carefully while they are still being designed.
The real discipline sits in the questions asked early.
In the assumptions challenged before they become dependencies.
In the access model staying close to purpose.
In trust being defined explicitly.
In data movement being understood before it becomes normal.
In observability being treated as part of architecture, not an afterthought.
This is how security architects design secure systems in practice.
They make structure visible early enough to shape it.
The Security Architect’s Blueprint
This is also the problem the Security Architect’s Blueprint was created to solve.
Too often, security architecture becomes a document set that looks complete but loses force when delivery pressure rises.
The Security Architect’s Blueprint turns that into a working system.
It connects architecture thinking, governance, assurance artefacts, and practical implementation guidance so that security architecture can survive real delivery conditions.
It helps architects and teams work through:
Trust boundary definition
Identity and access structure
Control placement
Architecture rationale
Governance-ready documentation
Implementation guidance for engineering
Evidence and assurance thinking
That is important because real delivery environments are busy. Timelines move. Dependencies multiply. Governance still needs traceability. Engineering teams still need clarity. Security still needs to hold.
Architecture has to survive all of that.
Final thought
Security architects design secure systems by shaping structure before weak assumptions become normal.
They look at how the system will really behave.
They follow identity.
They define trust boundaries.
They trace data flow.
They decide where controls will actually matter.
They make sure the system can still be observed and governed once it is live.
That is what makes the difference.
A system does not become secure because controls exist somewhere in a document library.
It becomes more secure when the architecture supports control from the beginning.
When that happens, security is no longer trying to fight the shape of the platform.
It becomes part of how the platform works.
Need help turning this into a working architecture?
Designing is one thing. Getting it to hold in real environments is another.
If you want Secure-by-Design architecture that is clear, implementable, and governance-ready:
View Secure-by-Design Advisory Service
Request a conversation
Understand How Secure Systems Are Actually Designed
Most security content focuses on tools.
This is about how systems are actually structured to handle trust, identity and risk.
I share practical insights on security architecture, secure system design and emerging threats.

