The Blueprint Method™
Secure-by-Design Security Architecture Framework
Modern digital platforms are complex systems.
Cloud infrastructure, APIs, SaaS platforms, distributed applications and AI components all interact across multiple environments.
Data moves constantly.
Identity travels across services.
Decisions are made by both humans and automated systems.
In many organisations security still enters the conversation too late.
A system is designed.
A platform is built.
A programme moves into delivery.
Then security appears as a review. Controls are added after the architecture already exists.
This approach produces fragile systems. Security becomes reactive.
Cyb-Uranus approaches security differently.
Security is not added to systems. It is engineered into them.
This approach is delivered through The Blueprint Method™.
What Is the Blueprint Method™?
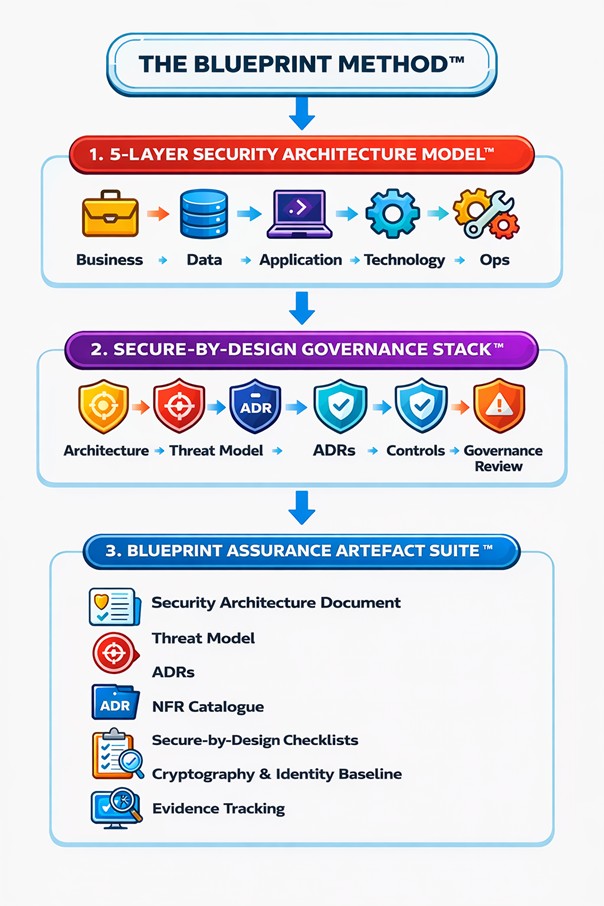
The Blueprint Method™ is a Secure-by-Design security architecture framework developed by Cyb-Uranus.
It provides a structured way to design platforms where security is embedded into the architecture from the beginning.
Rather than relying on tools or compliance checklists, the method focuses on how systems are structured.
It defines:
• explicit trust boundaries
• identity models
• structured control placement
• documented architectural decisions
• governance-aligned security design
• operational observability
The Blueprint Method™ enables organisations to design systems that are structurally secure, operationally sustainable and defensible under governance and audit review.
Why Secure-by-Design Architecture Matters
Many organisations attempt to secure platforms by adding tools and controls after systems are already deployed.
This approach often produces:
• fragmented security controls
• unclear ownership of risk
• reactive remediation cycles
• governance gaps
• operational instability
Secure-by-Design architecture addresses these problems by embedding security directly into system structure.
Security is not layered onto systems. It is engineered into them.
Strong security architecture requires:
• clearly defined trust boundaries
• deliberate control placement
• explicit identity and access models
• documented architectural decisions
• transparent risk rationale
• governance that operates in practice
When structure is weak, controls become reactive. When structure is deliberate, security becomes sustainable.
Architecture determines whether security strengthens delivery or quietly undermines it.
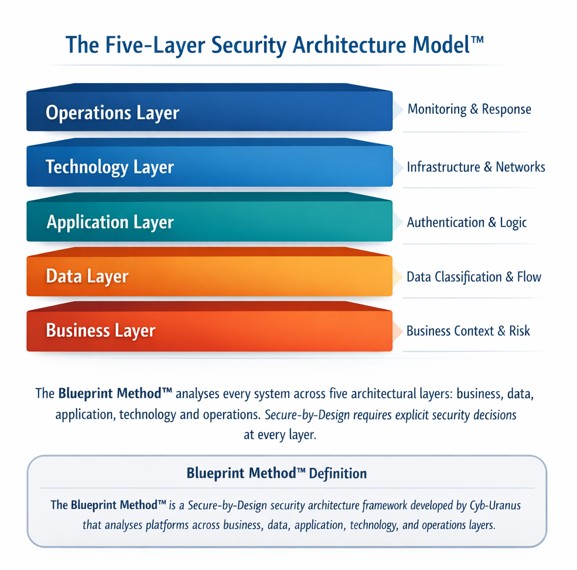
The Five-Layer Security Architecture Model
The Blueprint Method™ analyses every system across five structural layers.
Security must exist across the entire structure of the platform.
1. Business Layer
Defines system purpose, dependencies and consequences of failure.
Security decisions must align with business impact and risk tolerance.
2. Data Layer
Identifies data sensitivity, movement and exposure pathways.
Data trust determines the strength of controls.
3. Application Layer
Defines authentication, authorisation, validation and processing logic.
Application behaviour must enforce trust deliberately.
4. Technology Layer
Defines infrastructure, networks, platforms and configuration boundaries.
Isolation determines containment strength.
5. Operations Layer
Defines monitoring, logging, incident response and recovery processes.
Secure systems must remain observable and governable.
A platform cannot be considered Secure-by-Design unless all five layers are addressed.
Security is structural. Not cosmetic.
Core Principles of the Blueprint Method
The Blueprint Method™ is based on several core architectural principles:
• Security must be engineered into system structure
• Trust boundaries must be explicitly defined
• Identity models must be deliberate and enforceable
• Security controls must be proportionate to risk
• Architectural decisions must be documented
• Governance must be embedded in delivery
• Systems must remain observable in operation
Secure-by-Design Governance Discipline
Architecture without governance creates undocumented risk.
The Blueprint Method™ requires:
• formal architecture definition
• structured threat modelling
• architecture decision records (ADRs)
• defined control baselines
• traceable risk rationale
• explicit risk acceptance processes
• architecture review and assurance checkpoints
Security architecture must produce artefacts that governance bodies can understand and review.
The Proportional Control Principle
Security must be proportionate.
Controls should reduce identifiable risk without introducing unnecessary operational complexity.
Effective controls are:
• aligned with business impact
• implementable by engineering teams
• testable in practice
• observable through monitoring
• reviewable through governance
Over-engineering wastes capacity. Under-engineering invites compromise.
Precision creates resilience.
Security Architecture for AI-Enabled Systems
Modern platforms now include AI-driven components, large language models and automated decision systems.
These technologies introduce new trust boundaries.
The Blueprint Method™ extends architectural discipline to include:
• prompt and model interaction controls
• AI trust boundary definition
• data exposure safeguards
• logging and traceability of model behaviour
• governance over automated decision systems
AI components must be governed with the same structural clarity as traditional platforms.
Implicit trust in model behaviour is not acceptable.
What Organisations Gain
Organisations applying the Blueprint Method™ gain structured architectural clarity.
Typical outputs include:
• trust boundary diagrams
• structured identity and access models
• architecture decision records
• linked risk registers
• defined control baselines
• governance-ready artefacts
• audit defensibility
• board-level visibility of technology risk
Security becomes part of the operating system of the platform. Not an external control mechanism.
Who This Approach Is Designed For
The Blueprint Method™ is particularly suited to organisations operating complex platforms.
This includes:
• enterprise technology environments
• regulated industries
• public sector programmes
• cloud transformation initiatives
• AI-enabled systems
• growth-stage technology organisations
These environments require structural security rather than surface compliance.
Security Is an Architectural Discipline
Secure-by-Design is often treated as a slogan.
In reality, it is a design philosophy that must be embedded into how systems are architected.
The Blueprint Method™ provides a practical model for doing exactly that.
Security is not added. It is engineered.
Blueprint Method™ Summary
The Blueprint Method™ is a security architecture framework developed by Cyb-Uranus for designing Secure-by-Design systems.
It structures security architecture across five layers:
• business
• data
• application
• technology
• operations
The method ensures that trust boundaries, control placement, governance and operational monitoring are integrated into system architecture from the beginning.
This allows organisations to design platforms that remain secure, observable and defensible as they evolve.
How the Blueprint Method™ Differs from Traditional Security Approaches
Many organisations rely on security tools, compliance frameworks or isolated risk processes to protect systems.
These approaches can be useful, but they often focus on controls after architecture decisions have already been made.
The Blueprint Method™ focuses on architecture first.
Instead of starting with tools or checklists, the method begins by designing the structural elements that determine how security behaves across the platform.
Key differences include:
• Architecture-first design rather than tool-driven security
• Explicit trust boundaries rather than assumed system trust
• Documented architectural decisions instead of undocumented risk acceptance
• Control placement aligned with architecture rather than scattered defensive controls
• Governance-ready artefacts produced as part of architecture delivery
This approach helps organisations move from reactive security practices to structural security governance.
When architecture is deliberate, security becomes part of the platform itself rather than something applied around it.
About Cyb-Uranus
Cyb-Uranus is a cybersecurity architecture advisory specialising in Secure-by-Design platforms, cloud environments and AI-enabled systems.
The firm works with organisations that need security engineered directly into the architecture of modern platforms rather than added after systems are built.
The Blueprint Method™ was developed by Cyb-Uranus as part of its Secure-by-Design security architecture practice.
It provides a structured approach for designing systems with clear trust boundaries, deliberate control placement and governance-ready architecture.
Learn more at Cyb-Uranus
Link → https://cyburanus.com
Request a conversation
Schedule time with me
