WHAT IS SECURITY ARCHITECTURE? A PRACTICAL GUIDE FOR MODERN SYSTEMS

If you ask ten people in cybersecurity what security architecture is, you will probably get ten different answers.
Some will talk about firewalls. Others will start listing security tools. Some will say it is about compliance frameworks.
And a few will describe diagrams and control models.
This confusion happens everywhere. Even inside organisations that invest heavily in security.
The phrase security architecture gets used a lot, yet many people never stop to define what it actually means.
I have seen security discussions where architecture is reduced to a list of products. A SIEM here. An EDR there. Maybe a CASB or identity platform.
That is not architecture.
Tools are useful. Some are excellent. Many organisations rely on them every day.
But tools alone do not create security.
What actually determines whether a system is secure is the structure of the system itself.
- How data moves.
- Where trust exists.
- Who can access what.
- Where controls sit.
- How identity works across the environment.
These decisions shape the security posture of a system long before the first tool is installed.
That is the world of security architecture.
Security architecture is the discipline that designs how security works across a system before the system even exists.
It is the thinking that shapes the system. And when that thinking is done well, security becomes part of the system itself.
Not something that gets bolted on later.
What Security Architecture Actually Means
The easiest way to understand security architecture is to think about buildings.
If someone decides to build a hospital, the first step is not buying doors or installing alarms.
An architect designs the structure.
- They decide where the entrances go.
- Where restricted areas sit.
- Where sensitive rooms must be located.
- Where corridors connect.
- Where security checkpoints should exist.
Only after the structure is defined do the physical controls appear.
Security architecture works the same way for digital systems. It defines how the system is structured so security can function properly.
This includes things like:
- how systems communicate
- how identities are managed
- how data moves through the environment
- where trust exists
- where controls must be placed
A system without architecture grows in whatever direction development happens to take.
A system with architecture grows with structure.
The difference between those two situations becomes very obvious once a system starts scaling.
When there is no architecture, organisations eventually reach a point where security teams are constantly reacting.
New tools appear. More monitoring is added. More alerts are generated.
But the underlying structure of the system remains messy. And messy systems are difficult to secure.
Security architecture focuses on the structure underneath the tools.
It answers questions like:
- How should identity work across this platform?
- Where should trust stop?
- How should data cross system boundaries?
- Which components should be isolated?
- Where do security controls need to exist?
These questions shape the system long before security tooling enters the picture.
Why Architecture Determines Security
Many security incidents look like failures of tools. In reality they are often failures of structure.
An attacker moves laterally across systems. A compromised credential unlocks too many services.
Sensitive data becomes accessible from parts of the system that were never meant to see it.
When you trace these problems back far enough, you usually discover that the architecture allowed it.
Maybe the trust boundary was too wide. Maybe identity controls were weak.
Maybe system segmentation never existed. Maybe sensitive workloads sat inside shared environments.
Tools cannot fix these structural issues. They can detect them. Sometimes they can slow them down.
But the architecture already determines what is possible.
This is why security architecture matters so much in modern environments.
Systems today are no longer simple. They span cloud platforms.
They include APIs. They rely on identity providers. They process data across multiple services.
They connect internal environments with external platforms. And many systems evolve quickly.
Features are added. Integrations appear. Workloads move.
When security architecture is absent, systems grow organically.
Over time they become complicated webs of services, permissions and connections.
Trying to secure that environment after the fact becomes extremely difficult.
Security architecture prevents that situation. It introduces structure early. It creates boundaries.
It defines how security controls work across the environment.
And it provides a blueprint that allows systems to grow without losing control.

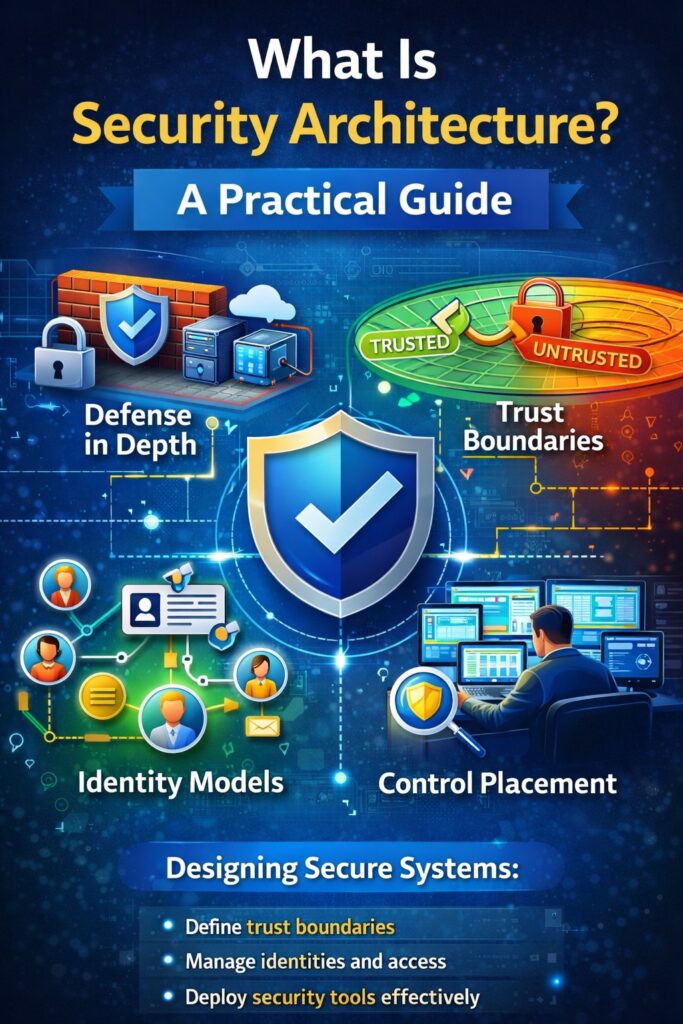
Core Elements of Security Architecture
Security architecture is built around several foundational concepts. These ideas appear across almost every modern architecture design.
Once you understand them, you begin to see them everywhere.
Trust Boundaries
One of the most important ideas in security architecture is the trust boundary.
A trust boundary is simply a point where the level of trust changes. Inside a boundary, components trust each other to a certain degree.
When something crosses that boundary, verification becomes necessary.
For example:
- A public user accessing a web application crosses a trust boundary when their request reaches the backend system.
- An internal service calling another service crosses a trust boundary if authentication is required.
- A cloud environment connecting to an internal network crosses a trust boundary.
Each boundary represents a place where controls must exist.
- Authentication.
- Validation.
- Monitoring.
- Filtering.
Without clearly defined trust boundaries, systems often treat too many components as trusted.
That creates opportunities for attackers to move through environments once a single entry point is compromised.
Good architecture identifies trust boundaries early and designs controls around them.
Identity Models
Identity is now the centre of most modern security models. Years ago, network boundaries played a bigger role.
Today systems operate across multiple networks, cloud environments and APIs.
Identity has become the control point that determines who or what can interact with a system.
A strong security architecture defines an identity model early.
This includes:
- how users authenticate
- how services authenticate
- how permissions are granted
- how identities are verified across systems
It also includes decisions around concepts like:
- Single Sign-On
- Federated identity
- Role-based access
- Service-to-service authentication
Identity models shape how access works across an entire platform. When identity is poorly designed, access control quickly becomes chaotic.
Permissions spread across systems. Service accounts gain excessive privileges. Access reviews become difficult.
A clear identity architecture keeps access predictable and manageable.
Control Placement
Another core concept is where security controls should live.
Security controls appear in many places:
- At the network level.
- Inside applications.
- Within identity systems.
- Within data platforms.
- Across monitoring environments.
Architecture determines the best location for these controls.
For example:
- Should authentication happen at the application layer?
- Should API gateways enforce access control?
- Should data protection happen inside storage services?
- Should monitoring occur centrally or across distributed components?
These decisions influence how effective security controls will be.
Poorly placed controls create blind spots. Well-placed controls protect systems without creating unnecessary complexity.
Governance
Security architecture also includes governance.
This part often receives less attention, yet it plays a vital role in keeping systems secure over time.
Governance defines how security decisions are made and maintained.
It includes things like:
- architecture standards
- design review processes
- security requirements for new systems
- control validation
- risk acceptance procedures
Without governance, even well-designed architectures eventually drift.
New services appear. Teams introduce shortcuts. Controls get bypassed.
Governance keeps the architecture aligned with security objectives as systems evolve.
How Security Architects Design Systems
When people hear the title Security Architect, they sometimes imagine someone installing security tools or reviewing vulnerability reports.
That is not the real job.
Security architects spend most of their time thinking about how systems should be structured before they exist.
A large part of the work happens during system design. This is the moment when the biggest security decisions are made.
At this stage, the architect begins asking questions such as:
- Where will users access the system from?
- Which components will communicate with each other?
- What type of data will the system process?
- Which components require the highest level of protection?
- How will identity work across the environment?
- Where do trust boundaries exist?
- How will data move across those boundaries?
These questions lead to architecture decisions.
For example, a system processing sensitive personal data may require:
- strong identity verification
- strict service authentication
- segmented workloads
- controlled API gateways
- centralised logging and monitoring
Another system might process lower-risk information but operate across many integrations. In that case, architecture decisions might focus more heavily on identity federation and API security.
The architect translates these requirements into a system structure. This structure is usually represented through architecture diagrams.
You might see diagrams showing:
- system components
- data flows
- security zones
- trust boundaries
- authentication paths
- control layers
These diagrams are not just visual aids. They help teams understand how the system behaves from a security perspective.
They also help identify weaknesses early.
For example, a simple architecture diagram can quickly reveal situations where:
- sensitive data crosses too many services
- authentication is missing between components
- external connections introduce risk
- monitoring visibility disappears at certain points
When these issues appear early, they are much easier to fix.
Once a system is already deployed and running in production, architectural changes become much harder.
This is why security architecture work usually happens before systems are built.
The goal is simple. Design systems that are secure by structure, not by accident.
Where the Blueprint Method™ Fits
Over time I noticed something interesting about security architecture discussions.
Many frameworks talk about controls. Many standards talk about policies.
Yet very few explain how architects should actually design secure systems step by step.
Security architects often rely on experience and scattered guidance. That gap is what led to the development of The Blueprint Method™.
The idea behind the Blueprint Method is straightforward. Security architecture should follow a clear sequence of thinking.
Instead of jumping straight into controls or tools, the architect starts by understanding the system itself.
- What the system does.
- How it processes data.
- Which components interact.
- Where trust boundaries appear.
Only after that structural understanding is complete do security controls enter the picture.
The Blueprint Method focuses on a series of core steps.
- First, understand the system purpose and data sensitivity.
- Second, map system components and interactions.
- Third, identify trust boundaries and risk surfaces.
- Fourth, design identity and access structures.
- Fifth, determine control placement across the architecture.
- Finally, ensure governance and monitoring exist to sustain the design.
This approach brings structure to architecture thinking.
It prevents teams from jumping directly into security tools without understanding the environment.
And it ensures security decisions align with how the system actually works. The result is architecture that supports security naturally.
Security becomes part of the system design instead of something applied later.
Why This Matters More Today
Security architecture has always been important. But modern systems have made it even more critical.
Organisations now operate across environments that did not exist twenty years ago.
- Cloud platforms.
- Distributed applications.
- Microservices.
- API ecosystems.
- Identity providers.
- Third-party integrations.
- Artificial intelligence services.
- Data pipelines.
Systems no longer sit neatly inside a single network. They span multiple platforms and services.
That complexity creates enormous flexibility. But it also increases the number of places where things can go wrong.
Without architecture, systems evolve into tangled networks of permissions, integrations and dependencies.
Security teams then spend enormous effort trying to monitor and contain the resulting risks.
Security architecture helps prevent this situation.
It provides a way to design systems where security remains understandable even as systems grow.
It introduces structure into environments that could otherwise become chaotic. And it allows organisations to scale technology without losing control of risk.

A Practical Way to Think About Security Architecture
A simple way to understand security architecture is to think about three core questions.
First: What are we protecting?
This usually involves identifying sensitive data, critical services and important operational capabilities.
Second: Where are the trust boundaries?
- These boundaries show where verification must happen.
- Where authentication is required.
- Where monitoring should occur.
Third: Where should controls live?
Controls need to exist at the points where they provide the most protection. Not randomly across the system.
When architects answer these questions clearly, the system structure begins to make sense.
Security becomes easier to reason about. Teams understand where protections exist and why they exist.
This clarity is one of the most valuable outcomes of security architecture.
Learn More
If you want to go deeper into how secure systems are designed in practice, I explore the full process in my book:
The Security Architect’s Blueprint
The book walks through the thinking process security architects use when designing secure systems, including:
- system structure
- trust boundary design
- identity models
- control placement
- architecture decision making
It is written for security professionals, architects, engineers and anyone interested in how modern secure systems are actually designed.
You can learn more here: The Security Architect’s Blueprint
Final Thoughts
Security architecture sits quietly underneath almost every modern digital system.
Users rarely see it. Executives may not think about it. Yet it determines how secure a system truly is.
Tools help. Policies help. Monitoring helps. But the structure of the system shapes everything that follows.
When security architecture is done well, security becomes part of how the system works.
When it is missing, organisations spend years trying to compensate.
Understanding security architecture is therefore one of the most valuable skills in modern cybersecurity.
It allows teams to move from reactive security toward systems that are secure by design. And that shift makes all the difference.
Understand How Secure Systems Are Actually Designed
Most security content focuses on tools.
This is about how systems are actually structured to handle trust, identity and risk.
I share practical insights on security architecture, secure system design and emerging threats.

