SECURE BY DESIGN ARCHITECTURE: SECURE SYSTEMS FROM THE START
How systems quietly break when security comes late
Most systems are not designed to be insecure. They just grow that way.
A team starts with a goal. Build something useful. Make it work. Get it into people’s hands.
So they move fast.
They pick services. They connect components. They get data flowing. They solve real problems.
And for a while, everything looks fine.
The system works.
Users can log in.
Data moves where it should.
The business gets value.
Then security comes in later.
Not because anyone ignored it. It’s just that it was not the first thing that shaped the system.
And this is where things start to bend.

When structure is already fixed
By the time security is introduced, the system already has a shape.
Connections already exist.
Access patterns are already in place.
Data is already flowing through paths that were never designed to be controlled.
At this point, security is no longer shaping the system. It is trying to catch up with it.
So what happens?
Controls get added on top.
Extra checks.
Additional rules.
Patches around decisions that have already settled into the design.
This creates tension, because the system was not built to support those controls cleanly.
You start to see things like:
- Shared accounts because identity was not defined properly
- Broad permissions because narrowing access would break functionality
- Unclear ownership because services grew without boundaries
- Data moving across components with no clear visibility
Nothing looks broken on the surface. But underneath, the system becomes harder to understand.
And when a system is hard to understand, it is hard to secure.
The slow spread of access
One of the first places this shows up is access.
In the early stages, access is simple. Someone needs to use the system, they are given permissions.
A service needs to call another service, it gets access.
Everything is driven by getting things working. But over time, those decisions stack.
Access grows wider.
Permissions become less precise.
Roles become harder to explain.
You start to hear things like:
- We cannot remove that permission, something might break
- That service needs broad access, we are not sure exactly what it uses
- This account is shared across multiple components
At that stage, access is no longer deliberate. It is inherited.
And inherited access is where risk starts to settle into the system quietly.
Identity is where clarity should start
Every action in a system comes from somewhere.
A user.
A service.
A workload.
If you cannot clearly answer who is doing what, the system starts to blur.
Late security often tries to fix identity after the fact.
You see layers added:
- Identity providers introduced after services are already connected
- Tokens passed around without clear ownership
- Service accounts reused across multiple functions
At this stage, identity becomes a patch. Not a foundation.
And when identity is unclear, everything built on top of it becomes harder to reason about.
You cannot confidently say:
- who initiated an action
- which component is responsible
- whether the behaviour is expected
This is where investigation becomes slow and frustrating, because the system cannot clearly tell its own story.
Trust boundaries that were never drawn
Every system has places where trust changes.
Between the internet and your application.
Between one service and another.
Between environments.
Between workloads and data.
These are not abstract ideas.
They are real points where decisions should be made.
Who is allowed in.
What is allowed through.
How interactions are controlled.
When systems are built without defining these boundaries early, everything starts to blend.
You end up with:
- Services talking freely without clear restrictions
- Internal components trusted more than they should be
- External inputs moving deeper into the system than expected
Once this is in place, trying to introduce boundaries later becomes difficult.
Because you are now cutting across an already connected system. And every boundary you introduce risks breaking something.
So boundaries become softer.
Exceptions get added.
Temporary decisions become permanent.
And the system carries that weight forward.
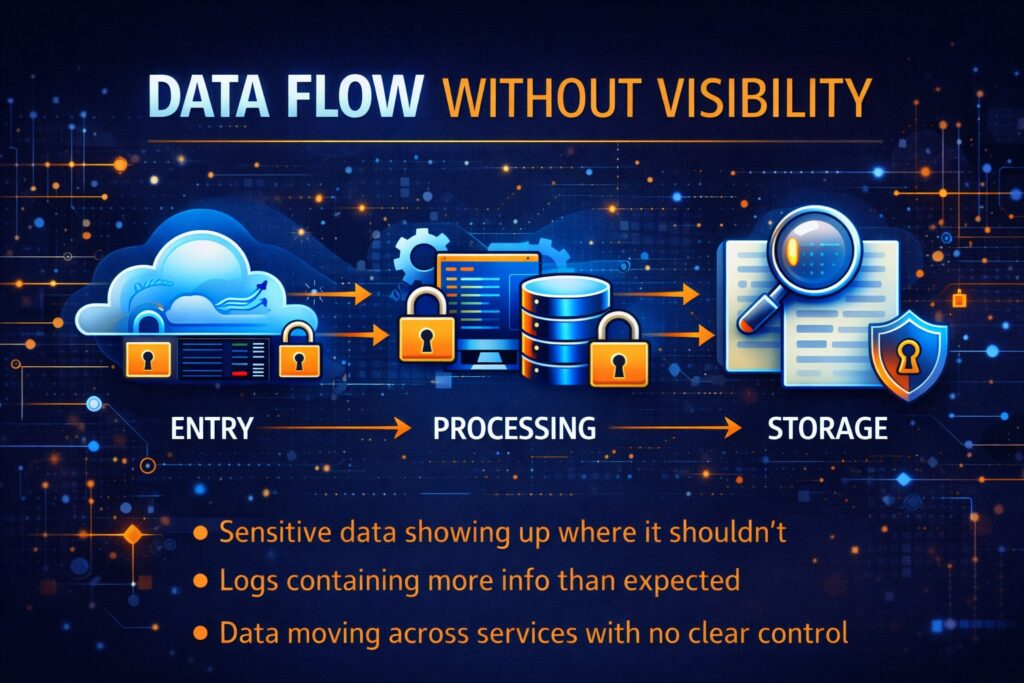
Data flow without visibility
Data is one of the clearest ways to understand a system.
Where it enters.
Where it moves.
Where it is stored.
Who can access it.
When this is not mapped early, data flow becomes something you discover later.
And discovery at that stage often brings surprises.
Sensitive data showing up in places it should not be.
Logs containing more information than expected.
Data moving across services without clear control.
Late security tries to trace this.
But tracing data after it has already spread is different from shaping its path from the beginning.
Because the routes already exist. And changing them affects the entire system.

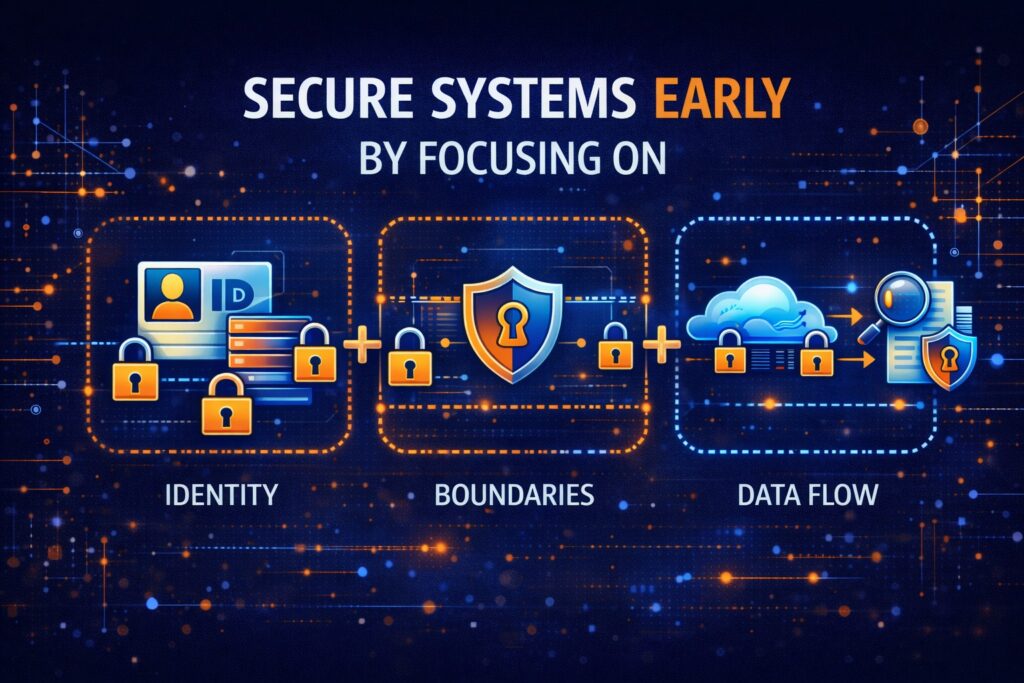
When security is introduced early
Now shift the timing.
Security is considered from the start. Not as a separate activity. But as part of how the system is shaped.
The difference is not loud. It shows up in small, deliberate decisions.
Decisions become clearer
When you think about security early, decisions slow down just enough to be intentional.
You start asking:
- Who needs access to this?
- What should this service be allowed to do?
- Where should this data live?
These are not blockers. They are design choices. And they guide how the system takes shape.
Instead of building first and adjusting later, the system grows with structure.
Access becomes deliberate
Access is no longer something that spreads. It is something that is defined.
Each component has a purpose.
Each identity has a scope.
Permissions are tied to behaviour, not convenience
This does not make the system rigid. It makes it understandable.
You can look at a component and know:
- what it can access
- what it cannot access
- why that decision exists
And when something changes, you adjust with clarity.

Behaviour becomes easier to follow
When identity is clear, boundaries are defined, and data flow is understood, the system starts to behave in a way that makes sense.
You can trace actions.
You can follow requests.
You can see how data moves through the system.
This matters more than people realise.
Because security is not just preventing issues. It is also being able to understand what is happening when something does occur.
A system that is easy to follow is easier to protect.
A light look at the layers shaping secure systems
When you step back and look across different systems, a pattern starts to appear.
It does not matter whether the platform is cloud-based, on-premise, API-driven or AI-enabled.
Secure systems tend to settle into a few consistent layers.
Not as theory but as structure.
Identity sits close to the centre
You need to know who or what is acting in the system.
Every request.
Every action.
Every decision.
If identity is unclear, everything else becomes harder.
Access control builds on that
Once identity is clear, access can be defined properly.
Not broad.
Not assumed.
Defined.
Each identity should only be able to do what it needs to do.
Nothing more.
System structure shapes interactions
This is where architecture becomes visible.
How components connect.
How services communicate.
How requests move.
This is where risk either spreads or gets contained.
Data protection follows the flow
Data does not sit still.
It moves.
And how it moves determines how it should be protected.
Storage matters.
Processing matters.
Exposure points matter.
Visibility ties everything together
You need to be able to see what is happening.
Not just collect logs.
Understand behaviour.
Trace actions.
Identify anomalies.
Follow activity across the system.
These layers are not separate.
They overlap.
They reinforce each other.
And when they are shaped early, the system feels different.
More stable.
More predictable.
Easier to work with.
Why teams need a practical way to apply this
Understanding this at a high level is one thing. Applying it in a real environment is something else.
Because real systems are not clean.
They come with:
- Existing components
- Delivery pressure
- Integration complexity
- Business constraints
And this is where many teams struggle.
They understand secure by design architecture. But they do not have a clear way to apply it consistently.
That is where structure becomes important.
The Blueprint Method™: making secure-by-design practical
That is exactly why The Blueprint Method™ was developed.
Not as theory.
As a working approach.
The Blueprint Method™ is a Secure-by-Design Security Architecture Framework created through Cyb-Uranus.
It was shaped for modern platforms where:
- Cloud infrastructure
- APIs
- SaaS platforms
- Distributed services
- AI-enabled components
all interact across multiple environments.
Data moves constantly.
Identity travels across services.
Decisions are made by both humans and automated systems.
And in many organisations, security still enters the conversation too late.
A system is designed.
A platform is built.
A programme moves into delivery.
Then security appears.
As a review.
As a control layer.
As something added on top..
That approach creates fragile systems.
Security becomes reactive.
Ownership becomes blurred.
Controls become fragmented.
Governance starts chasing decisions that should have been made earlier.
The Blueprint Method™ was built to deal with that directly.
It provides a structured way to design platforms where security is embedded into the architecture from the beginning.
The focus is on structure. Not on adding more noise.
It defines:
- explicit trust boundaries
- identity models
- structured control placement
- documented architectural decisions
- governance-aligned security design
- operational observability
Because a platform does not stay secure just because controls exist.
It stays secure when those controls are supported by structure.
The five layers behind the method
The Blueprint Method™ looks at security architecture across five connected layers.
1. Business Layer
This defines the purpose of the system.
Why it exists.
What it supports.
What failure would mean.
Security decisions should make sense in that context.
2. Data Layer
This focuses on what data exists and how it moves.
What is sensitive.
Where it flows.
Where it is exposed.
Data trust shapes control strength.
3. Application Layer
This is where behaviour is enforced.
Authentication.
Authorisation.
Validation.
Processing logic.
This layer decides how trust is applied in practice.
4. Technology Layer
This covers infrastructure and platform boundaries.
Networks.
Compute.
Services.
Configuration.
This is where isolation and containment live.
5. Operations Layer
This is how the system is observed and managed.
Monitoring.
Logging.
Incident response.
Recovery.
A system must remain understandable when it is live.
A platform cannot be called secure-by-design if only one or two of these layers are considered.
Security runs through all of them.
It is structural.
Not cosmetic.
Extending this into AI-enabled systems
Modern systems are changing.
AI components are now part of real platforms.
That introduces new considerations:
how models are accessed
how prompts interact with systems
how data is exposed
how decisions are made
These are new trust boundaries.
They need the same level of clarity.
The same level of structure.
The Blueprint Method™ extends into this space by bringing:
- defined AI trust boundaries
- control over model interactions
- data exposure safeguards
- traceability of behaviour
- governance over automated decisions
AI cannot sit outside architecture discipline.
It has to be part of it.
What this looks like in real systems
You can usually feel the difference when you step into a real environment.
Systems built with late security
They tend to carry:
- access patterns that no one wants to touch
- unclear service interactions
- data flows that are only partially understood
Teams spend time working around the system.
Adding controls.
Investigating incidents.
Trying to reduce risk without breaking functionality.
Systems built with secure-by-design thinking
They feel different.
Changes are easier to make.
Access is easier to review.
Issues are easier to trace.
The system supports the controls.
Not the other way around.
Taking this into real systems
It is one thing to understand this. It is another to apply it.
Because real systems are not starting from zero.
Start where the system reveals itself
Before thinking about controls, tools, or frameworks, look at how the system behaves.
Not diagrams first.
Not documentation first.
Behaviour.
Ask simple questions:
- Who interacts with the system?
- What happens when they do?
- What components respond?
- Where does the data go next?
This is where the truth of the system sits.
Map interactions before adding controls
Most security issues are not caused by missing tools. They come from interactions that were never properly understood.
So instead of jumping straight into controls, map how things connect.
Keep it simple.
Users → application
Application → API
API → database
Services → other services
External systems → internal components
You are not trying to document everything.
You are trying to see:
- where interactions happen
- how often they happen
- what kind of data is involved
This is where risk starts to show up naturally. Because you can now see movement.
Define identity at every interaction point
Now look at each interaction.
Ask one question: Who or what is making this call?
Be precise. Not the system. Not the backend.
Be specific.
- Is it a user?
- Is it a service?
- Is it a scheduled job?
- Is it a third-party integration?
Every interaction should have a clear identity. And that identity should be unique to its purpose.
This is where many systems drift. Because identities get reused.
A single service account starts handling multiple responsibilities.
Tokens are shared across components. Access keys are passed around to make things easier.
That convenience builds confusion. And confusion spreads risk quietly.
When identity is clean, everything else becomes easier to shape.
Place trust boundaries deliberately
Once interactions and identities are clear, you can start to place boundaries.
Imagine the boundaries as points where you pause and decide:
- What do I trust here?
- What do I need to check?
You will usually find natural boundary points:
Internet → application
Application → internal services
Services → data stores
Internal → external integrations
At each boundary, define:
- what is allowed through
- how it is validated
- how it is monitored
Do not overcomplicate this. Clarity matters more than complexity.
A simple, well-defined boundary is stronger than a complex one filled with exceptions.
Shape data flow intentionally
Now follow the data. Pick a piece of information and trace it.
Where does it enter?
Where is it processed?
Where is it stored?
Where is it exposed?
You will often notice something: Data moves more than expected.
It appears in logs.
It gets cached.
It gets passed to services that do not need it.
This is where design decisions matter.
You can:
- reduce unnecessary movement
- limit exposure
- keep sensitive data closer to controlled components
When data flow is shaped early, protection becomes part of the system.
When it is shaped late, protection becomes a constant effort.
Place controls where they belong
At this point, you are not guessing where controls should go. The system shows you.
Controls sit at:
- identity points such as authentication and service identity
- boundaries such as validation, filtering and inspection
- data handling points such as encryption, masking and storage controls
- visibility points such as logging, monitoring and tracing
You are no longer placing controls randomly. You are placing them where the system actually needs them.
And that is a big shift. Because it reduces noise. And increases effectiveness.
What this looks like in a cloud system
Let’s make this more concrete. Imagine a simple cloud-based application.
A user logs in through a web interface.
The application calls backend services.
Services interact with a database and external APIs.
This is where secure-by-design thinking shapes the system differently.
Identity
Instead of a shared backend identity:
- each service has its own identity
- user identity is clearly separated from service identity
- tokens are scoped to specific actions
Now when something happens, you know exactly who or what initiated it.
Trust boundaries
Instead of everything inside the cloud environment being trusted:
- the internet boundary is clearly defined
- internal service boundaries are treated with care
- external integrations are isolated and validated
Now trust is not assumed. It is defined.
Data flow
Instead of data moving freely:
- sensitive data is only handled by specific services
- logs are controlled to avoid exposure
- data storage locations are deliberate
Now data movement is predictable.
Access control
Instead of broad permissions:
- each service only has access to what it needs
- roles are tied to function
- permissions are easier to review
Now access reflects behaviour.
Visibility
Instead of fragmented logging:
- actions are traceable across components
- identity is linked to activity
- unusual behaviour stands out
Now the system can explain itself.
The Security Architect’s Blueprint: making this practical
This is also why I created the Security Architect’s Blueprint.
Because security architecture often fails for one simple reason.
It turns into documentation.
Documents are written.
Diagrams are produced.
Controls are listed.
Then delivery pressure arrives. And the architecture fades.
Security becomes reactive again.
The Security Architect’s Blueprint was created to solve that problem.
It is a practical system for designing secure-by-design platforms in a way that stays usable, reviewable, and defensible in real environments.
It connects three things that are often treated separately:
1. Structured design thinking
Through the Blueprint Method™, systems are shaped across five layers:
Business, Data, Application, Technology, Operations
Each layer forces clearer decisions around risk, trust boundaries, identity, control placement, and operational behaviour.
2. Governance that actually connects
Architecture decisions are tied to:
- threat modelling
- architecture decision records
- control baselines
- assurance evidence
So security is not just designed. It is explainable and reviewable.
3. Delivery that teams can use
The Blueprint translates into practical artefacts:
- Security requirements
- Control baselines
- Implementation checklists
- Architecture guidance
- Assurance tracking
Because engineering teams do not need more theory. They need something they can apply.
This is especially useful across cloud platforms, APIs, distributed systems, data platforms, and AI-enabled environments where complexity grows quickly.
At its core, the goal is simple.
To keep security architecture present when real delivery pressure begins.
Because if it disappears at that point, everything falls back into reactive fixes.
And by then, the structure is already set. Blueprint is there to support.
When you are working with an existing system
Not every system starts clean.
Most of the time, you are walking into something that already exists. This is where people feel stuck.
Because the system already has:
- shared identities
- unclear boundaries
- scattered data flow
You cannot rebuild everything overnight. But you can start to reshape it.
Start by reducing confusion
Pick one area.
Identity is usually a good place.
Ask:
- Where are identities shared?
- Where can they be separated?
Even small changes help.
Splitting one shared account into two clear identities creates clarity. And that clarity spreads.
Introduce boundaries gradually
You do not need to define every boundary at once. Start with the most exposed points.
Internet-facing components.
External integrations.
Define clear rules there. Then move inward.
Over time, the system becomes easier to control.
Clean up data flow in stages
Look for obvious issues first.
Sensitive data in logs.
Unnecessary duplication.
Data flowing to components that do not need it.
Fix those. Then refine further.
You do not need perfection. You need direction.
Why teams struggle with this
It is not because it is complex. But because it requires a shift in how people think.
Teams are used to:
- building first
- fixing later
- adding controls as needed
Secure by design architecture asks for:
- thinking earlier
- deciding with intent
- shaping structure before it hardens
That feels slower at first. But it saves time later. Because you are not constantly correcting the system.
The long-term effect
Over time, the difference becomes obvious.
Systems built with secure-by-design thinking:
- are easier to understand
- are easier to change
- carry less hidden risk
Teams spend less time firefighting.
More time building.
And that is where the real value sits.
Final thought
When you look at a system, do not start with tools.
Start with structure.
Look at identity.
Look at boundaries.
Look at data flow.
Those three will tell you more about the system than any security tool ever will.
And once those are clear, everything else starts to fall into place.
Understand How Secure Systems Are Actually Designed
Most security content focuses on tools.
This is about how systems are actually structured to handle trust, identity and risk.
I share practical insights on security architecture, secure system design and emerging threats.

