CLOUD SECURITY ARCHITECTURE: HOW SECURE CLOUD SYSTEMS ARE DESIGNED
Cloud security gets talked about a lot.
Usually the conversation goes straight to tools.
Identity tools.
Cloud security platforms.
Monitoring tools.
Firewalls.
Encryption.
All important. But that is not where secure cloud systems begin.
A cloud system can have all the right tools on paper and still be difficult to secure. Another can use fewer tools and still be far more controlled. The difference is usually not the product stack. It is the structure underneath it.
That structure is cloud security architecture.
And this is the part many articles skip.
They give long lists of services and best practices, but they do not explain how architecture decisions shape the security of the whole environment. They do not explain why one design creates control and clarity, while another creates sprawl, blind spots and constant firefighting.
That is the real issue.
Cloud security architecture is not a shopping list. It is the way a cloud system is designed so security works properly across the whole environment.
That includes how identity is handled, how services communicate, where trust begins and ends, how data moves, where controls sit, and how the environment is observed over time.
Once you understand that, cloud security starts to make a lot more sense.
What cloud security architecture actually means
Cloud security architecture is the security structure of a cloud system.
That structure decides how the system behaves.
Who can access what.
How requests are verified.
Which services can talk to each other.
How data is protected.
Where controls apply.
What is monitored.
Before any setting is turned on, before any dashboard lights up, those design decisions already shape the security posture of the system.
That is why cloud architecture matters so much.
Two organisations can both be running on AWS. Both can be using managed services. Both can have logging, identity controls and network protections. Yet one environment feels controlled and understandable, while the other feels messy and exposed.
The cloud platform is not the difference. The design is.
That is why I always come back to architecture first. Tools matter, but they only make sense once the structure is clear.
Why cloud made architecture even more important
In older environments, the network did a lot of the heavy lifting.
Systems sat in clearer boundaries.
Internal and external were easier to distinguish.
The perimeter had more meaning.
Cloud changed that. Now systems are more distributed.
Applications are split across services.
Users connect from different locations.
APIs connect internal and external components.
Managed services process and store data in ways teams do not always see directly.
Infrastructure changes faster than it used to.
That flexibility is one of the biggest strengths of cloud.
It is also why architecture matters more.
You can no longer depend on location alone. You cannot assume that because something sits inside an environment it should be trusted. You cannot rely on broad access patterns and expect that to hold up as systems scale.
Cloud removes a lot of old assumptions.
That means the system needs stronger design.
When the architecture is clear, security scales more naturally. When it is not, security teams spend their time trying to patch over structural problems with more controls and more effort.
The shift from infrastructure thinking to system thinking
One of the biggest mindset shifts in cloud security is moving away from infrastructure-only thinking.
A lot of security conversations still begin with servers, networks and tools. That is understandable. Those things are still important.
But secure cloud design requires a wider view.
You need to understand the whole system.
What the application does.
What data matters.
Which identities are involved.
How services interact.
Where decisions are made.
Which flows are sensitive.
That is because cloud security is no longer just protecting infrastructure. It is protecting interactions across a living system.
That is why secure cloud architecture is really system design with security built into it from the start.
The core parts of a secure cloud architecture
When I look at a cloud system, there are a few things I want to understand early. These are the things that usually tell you whether the system is likely to remain understandable and secure as it grows.
Identity at the centre
Identity sits at the heart of cloud security.
Not the network.
Not the location.
Identity.
Users have identities. Applications have identities. Services have identities. Workloads have identities. Secure cloud systems make identity central because every action should tie back to something known.
That means thinking about questions like:
How do users authenticate?
How do administrators authenticate?
How do services prove who they are to each other?
How is privileged access controlled?
How are temporary and machine identities handled?
When identity is clear, access becomes easier to reason about.
When identity is weak or messy, everything else becomes harder.
Trust boundaries
Cloud systems are full of connections.
A user connects to an application.
An application calls an API.
An API reaches a data store.
A workload uses a managed service.
Each of these interactions crosses some kind of boundary.
A trust boundary is simply a point where trust changes and something needs to be verified, limited, or monitored.
In secure cloud design, these boundaries are not left vague. They are designed deliberately.
Between the internet and the application.
Between public-facing and internal services.
Between workloads and data stores.
Between one environment and another.
Between production and non-production.
The clearer those boundaries are, the easier it is to place the right controls in the right places.
Service-to-service communication
This part gets overlooked far too often.
Modern cloud systems depend heavily on service-to-service communication. One component hardly works alone. Systems are made up of APIs, functions, queues, containers, data platforms and managed services all interacting in the background.
If that communication is not designed carefully, risk spreads quietly.
Secure cloud architecture pays close attention to:
how services authenticate
what permissions they have
what they can call
what they should never reach
how those calls are observed
This is where broad permissions can become dangerous. A single over-permissioned service can create far more exposure than people realise.
Data flow and data handling
Data is one of the fastest ways to understand how secure a cloud design really is.
Where does data enter?
Where is it processed?
Where is it stored?
Which services can see it?
Which environments contain copies?
What leaves the system?
Secure cloud design treats data movement as something to be understood and controlled.
That includes encryption, yes, but it also includes design decisions around separation, minimisation, access paths, retention, backups and integration points.
A system becomes much easier to secure when the data flows are clear.
Control placement
Controls work best when they sit close to the risk they are meant to manage.
Authentication belongs where access begins.
Authorisation belongs where decisions are made.
Validation belongs where data enters.
Monitoring belongs where important events happen.
When controls are placed thoughtfully, the system works with them.
When controls are scattered, duplicated, or applied in the wrong places, they create confusion without necessarily improving security.
This is one reason architecture matters so much. It helps you decide not just which controls matter, but where they should live.
Visibility
A secure cloud system should not feel mysterious.
You should be able to understand what is happening.
Who accessed what.
Which service called which dependency.
What changed.
Which behaviour looks unusual.
Visibility is not just collecting logs. It is also designing the environment so meaningful observation is possible.
That includes logging, monitoring and alerting, as well as making sure the architecture itself supports traceability and understanding.

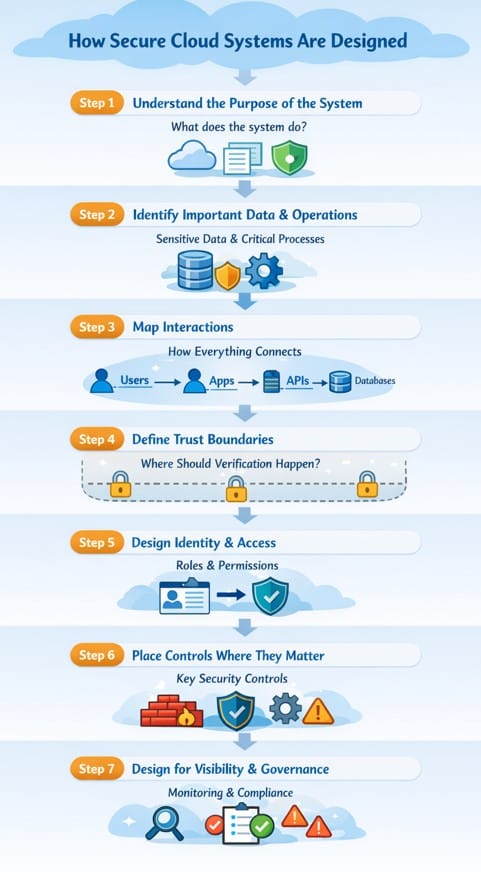
How secure cloud systems are designed
When I approach cloud security architecture, I do not start with a list of tools. I start with the system.
Step 1: Understand the purpose of the system
What does the system do?
That sounds obvious, but it matters more than people think.
A platform processing public content has different risks from one handling customer records or sensitive case data. A simple internal workflow system has different concerns from an internet-facing SaaS platform.
You need to understand the purpose before you can shape the protection.
Step 2: Identify the important data and operations
What really matters here?
Sensitive data
critical business processes
privileged actions
high-risk integrations
These are often the parts of the system where stronger controls need to sit.
Step 3: Map interactions
Cloud systems are interaction-heavy.
A secure design starts to emerge when you map how everything connects.
Users to apps.
Apps to APIs.
APIs to databases.
Workloads to managed services.
External systems to internal components.
This is where structure becomes visible.
Step 4: Define trust boundaries
Once the interactions are visible, the next step is to decide where trust should stop and where verification needs to happen.
This is where architecture becomes very practical.
It is one thing to say verify access. It is another to decide exactly where that verification lives and how it supports the flow of the system.
Step 5: Design identity and access properly
This is where many important cloud decisions sit.
Role design
privilege boundaries
service identities
admin paths
segregation of duties
access review patterns
Good identity and access design reduces exposure across the whole environment.
Step 6: Place controls where they matter most
This is where the security model becomes tangible.
Controls at entry points
controls at service layers
controls around data access
controls around privileged actions
controls around change and deployment paths
The goal is not to add more for the sake of it. The goal is to support the structure of the system with the right protections.
Step 7: Design for visibility and governance
A cloud system is not secure just because it was well designed once.
It changes.
That means governance matters.
Who approves changes?
How are new services introduced?
How is drift identified?
How are risky configurations detected?
How are incidents investigated?
Cloud security architecture includes this operational thinking from the beginning.
AWS security architecture and Azure security architecture
People often ask whether AWS security architecture and Azure security architecture are fundamentally different.
The services and terminology differ, yes.
But the deeper thinking remains the same.
You still need strong identity design.
You still need clear trust boundaries.
You still need controlled service communication.
You still need deliberate access control.
You still need visibility.
That is why good architecture thinking transfers across cloud platforms.
The names change.
The principles do not.
This matters because too much cloud advice is written as if security depends entirely on knowing the latest service names. It does not. The tools and services matter, but the architecture thinking underneath them matters more.
Where cloud security design starts to go wrong
A few patterns show up again and again when cloud environments become difficult to secure.
Broad access paths.
Too many services able to reach too much data.
Poorly controlled administrative access.
Weak service identity design.
Limited visibility across interactions.
Growth without clear trust boundaries.
None of these problems are solved by reading out a longer list of tools. They are design problems first.
That is why secure cloud systems feel different. They feel intentional. You can follow the logic of how they work.
A simple way to think about cloud security architecture
If you strip the whole thing back, secure cloud design comes down to a few practical questions:
Do we know who or what is making this request?
Should it be allowed?
What exactly should it be allowed to do?
Where does trust change?
Can we see what is happening?
Can this grow without losing control?
Those questions get you much closer to secure cloud architecture than a long product comparison ever will.
Where the Blueprint Method™ fits
This is exactly why structured design thinking matters.
The Blueprint Method™ follows a clear sequence:
Understand the system.
Map the interactions.
Define the trust boundaries.
Design identity carefully.
Place controls where they matter.
Build visibility and governance in from the start.
Cloud does not remove the need for architecture. It increases it.
The more dynamic the environment becomes, the more valuable clear structure becomes.
Final thoughts
Cloud security architecture is not a side topic.
It is the design foundation that determines whether a cloud environment remains understandable, controllable and secure over time.
The best cloud systems do not feel secure because they have the longest list of tools. They feel secure because the structure makes sense.
Identity is handled properly.
Access is controlled deliberately.
Trust boundaries are clear.
Service communication is understood.
Data flows are visible.
Controls sit where they matter.
That is what secure cloud design looks like in practice.
And once you start looking at cloud systems through that lens, a lot of things become easier to see.
Learn More
If you want to understand how secure systems are designed in practice, I explain the full thinking process in:
The Security Architect’s Blueprint
Understand How Secure Systems Are Actually Designed
Most security content focuses on tools.
This is about how systems are actually structured to handle trust, identity and risk.
I share practical insights on security architecture, secure system design and emerging threats.

